Navigation
- RADIUS Overview
- Two-factor Policies Summary
- Create Two-factor Policies
- Bind Two-factor Policies to Gateway
RADIUS Overview
For two-factor authentication using Azure Multi-factor Authentication, see Jason Samuel How to deploy Microsoft Azure MFA & AD Connect with Citrix NetScaler Gateway
Citrix CTX125364 How to Configure Dual Authentication on NetScaler Gateway Enterprise Edition for Use with iPhone and iPad.
Some two-factor products (e.g. SMS Passcode) require you to hide the 2nd password field. Receiver 4.4 and newer supports hiding the 2nd field if you configure a Meta tag in index.html.
- CTX205907 Dual-Password Field Shows in First Authentication When Connecting to NetScaler Gateway from Windows Receiver for instructions.
- CTX203775 Citrix Receiver and 2-Step Verification Incompatibility 💡
Two-factor authentication to NetScaler Gateway requires the RADIUS protocol to be enabled on the two-factor authentication product.
On your RADIUS servers, you’ll need to add the NetScaler appliances as RADIUS Clients. When NetScaler uses a local (same appliance) load balanced Virtual Server for RADIUS authentication, the traffic is sourced from the NetScaler SNIP (Subnet IP). When NetScaler uses a direct connection to a RADIUS Server without going through a load balancing Virtual Server, or uses a remote (different appliance) Load Balancing Virtual Server, the traffic is sourced from the NetScaler NSIP (NetScaler IP). Use the correct IP(s) when adding the appliances as RADIUS Clients. And adjust firewall rules accordingly.
For High Availability pairs, if you locally load balance RADIUS, then you only need to add the SNIP as a RADIUS Client, since the SNIP floats between the two appliances. However, if you are not locally load balancing RADIUS, then you’ll need to add the NSIP of both appliances as RADIUS Clients. Use the same RADIUS Secret for both appliances.
Two-factor Policies Summary
When configuring the NetScaler Gateway Virtual Server, you can specify both a Primary authentication policy, and a Secondary authentication policy. Users are required to successfully authenticate against both policies before being authorized for NetScaler Gateway.
For browser-based StoreFront, you need two authentication policies:
- Primary = LDAPS authentication policy pointing to Active Directory Domain Controllers.
- Secondary = RADIUS authentication policy pointing to RSA servers with RADIUS enabled.
For Receiver Self-service (native Receiver on mobile, Windows, and Mac), the authentication policies are swapped:
- Primary = RADIUS authentication policy pointing to RSA servers with RADIUS enabled.
- Secondary = LDAPS authentication policy pointing to Active Directory Domain Controllers.
If you need to support two-factor authentication from both web browsers and Receiver Self-Service, then you’ll need at least four authentication policies as shown below.
Primary:
- Priority 90 = RADIUS policy. Expression = REQ.HTTP..HEADER User-Agent CONTAINS CitrixReceiver
- Priority 100 = LDAP policy. Expression = REQ.HTTP..HEADER User-Agent NOTCONTAINS CitrixReceiver
Secondary:
- Priority 90 = LDAP policy. Expression = REQ.HTTP..HEADER User-Agent CONTAINS CitrixReceiver
- Priority 100 = RADIUS policy. Expression = REQ.HTTP..HEADER User-Agent NOTCONTAINS CitrixReceiver
Create Two-factor Policies
Do the following to create the Two-factor policies:
- Create an LDAP server.
- For RADIUS, on the left, expand Authentication, and click Dashboard.
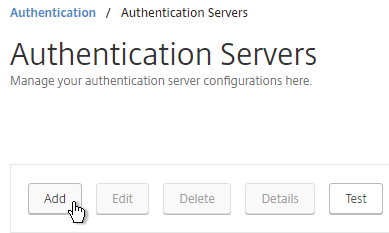
- On the right, click Add.
- Change Choose Server Type to RADIUS.
- Give the server a name.
- Specify the IP address of the RADIUS load balancing Virtual Server.
- Enter the secret key specified when you added the NetScalers as RADIUS clients on the RADIUS server. Click Test Connection.
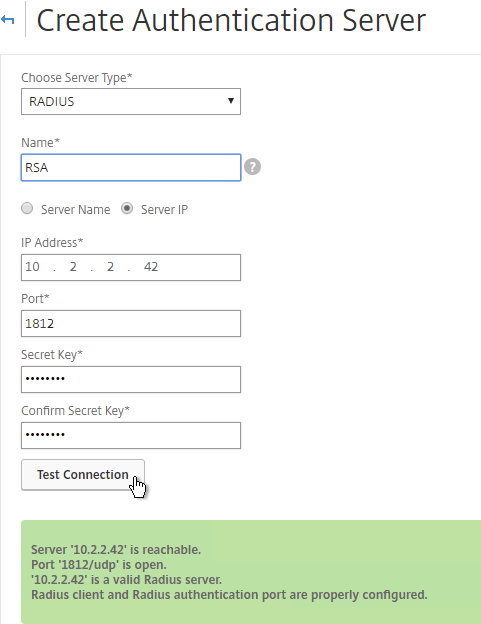
- Scroll down and click Create.
add authentication radiusAction RSA -serverIP 10.2.2.210 -serverPort 1812 -radKey Passw0rd
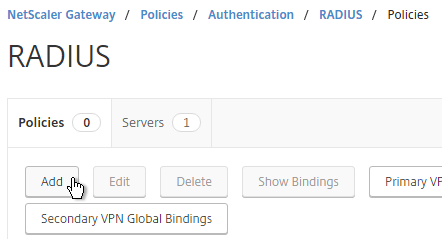
- Since you can’t create authentication policies from the authentication dashboard, go to NetScaler Gateway > Policies > Authentication > RADIUS.
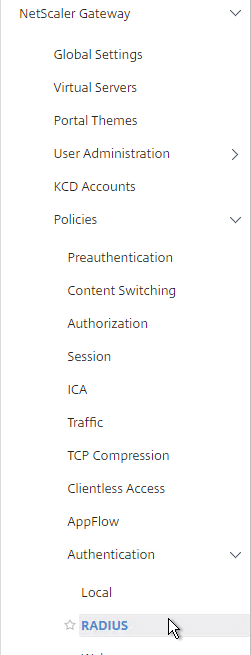
- On the right, in the Policies tab, click Add.
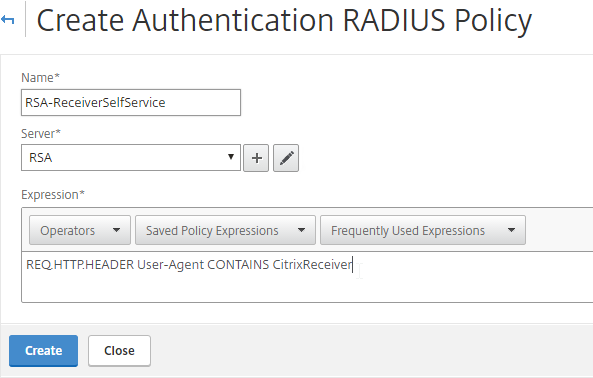
- Name it RSA-ReceiverSelfService or similar.
- Select the RADIUS server created earlier.
- Enter an expression. You will need two policies with different expressions. The expression for Receiver Self-Service is REQ.HTTP.HEADER User-Agent CONTAINS CitrixReceiver.
- Click Create.
add authentication radiusPolicy RSA-ReceiverForWeb "REQ.HTTP.HEADER User-Agent NOTCONTAINS CitrixReceiver" RSA add authentication radiusPolicy RSA-ReceiverSelfService "REQ.HTTP.HEADER User-Agent CONTAINS CitrixReceiver" RSA add authentication ldapPolicy Corp-Gateway-ReceiverForWeb "REQ.HTTP.HEADER User-Agent NOTCONTAINS CitrixReceiver" Corp-Gateway add authentication ldapPolicy Corp-Gateway-ReceiverSelfService "REQ.HTTP.HEADER User-Agent CONTAINS CitrixReceiver" Corp-Gateway
- Create another policy to match the ones shown below. Both RADIUS policies are configured with the same RADIUS server. The only difference between them is the expression (CONTAINS vs NOTCONTAINS):
Name Expression Server RSA-ReceiverSelfService REQ.HTTP.HEADER User-Agent CONTAINS CitrixReceiver RSA RSA-ReceiverForWeb REQ.HTTP.HEADER User-Agent NOTCONTAINS CitrixReceiver RSA 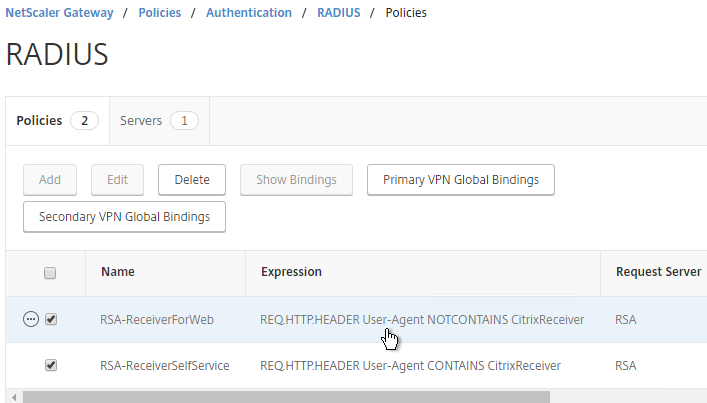
- Go to the NetScaler Gateway\Policies\Authentication\LDAP node.
- On the Policies tab, create two policies with the expressions shown below. Both LDAP policies are configured with the same LDAP server. The only difference between them is the expression (CONTAINS vs NOTCONTAINS).
Name Expression Server LDAP-Corp-ReceiverSelfService REQ.HTTP.HEADER User-Agent CONTAINS CitrixReceiver LDAP-Corp LDAP-Corp-ReceiverForWeb REQ.HTTP.HEADER User-Agent NOTCONTAINS CitrixReceiver LDAP-Corp 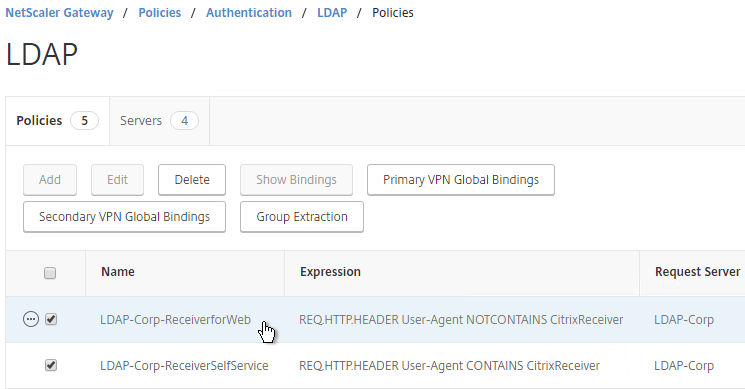
Bind Two-factor Policies to Gateway
- When you create or edit a NetScaler Gateway Virtual Server, bind the policies as shown in the following table. Priority doesn’t matter because they are mutually exclusive.
Policy Name Type Bind Point LDAP-Corp-ReceiverForWeb LDAP Primary RSA-ReceiverSelfService RADIUS Primary LDAP-Corp-ReceiverSelfService LDAP Secondary RSA-ReceiverForWeb RADIUS Secondary 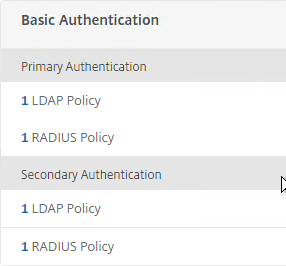
bind vpn vserver gateway.corp.com -policy Corp-Gateway-ReceiverForWeb -priority 100 bind vpn vserver gateway.corp.com -policy RSA-ReceiverSelfService -priority 110 bind vpn vserver gateway.corp.com -policy RSA-ReceiverForWeb -priority 100 -secondary bind vpn vserver gateway.corp.com -policy Corp-Gateway-ReceiverSelfService -priority 110 -secondary
- The session policy for Receiver Self-Service needs to be adjusted to indicate which authentication field contains the Active Directory password. On the Client Experience tab is Credential Index. This needs to be changed to SECONDARY. Leave the session policy for Web Browsers set to Primary.
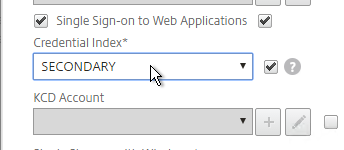
set vpn sessionAction "Receiver Self-Service" -ssoCredential SECONDARY
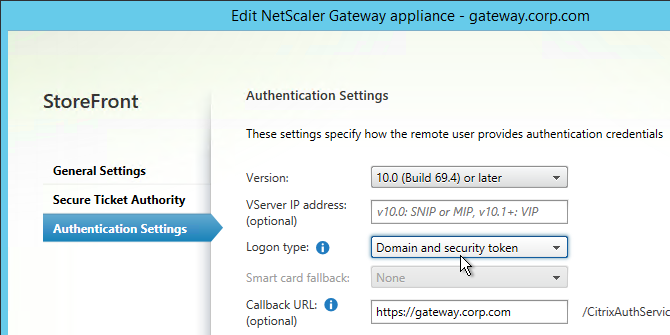
- On the StoreFront server, when creating the NetScaler Gateway object, change the Logon type to Domain and security token.
I know this is an older post, but very curious about something….
For Receiver Self-service (native Receiver on mobile, Windows, and Mac), the authentication policies are swapped:
Primary = RADIUS authentication policy pointing to RSA servers with RADIUS enabled.
Secondary = LDAPS authentication policy pointing to Active Directory Domain Controller
**Why are the authentication policies swapped for Receiver Self-Service?
I suspect a developer messed up long ago and then it became too late to swap the fields in a later release. nFactor fixes the swapping issue.
Hi Carl,
is there a way we can have a drop down selection on the login page to choose between Push and PIN for MFA as there are certain countries that dont allow push. im running 11.1 code
Hi Carl,
I want to use RADIUS auth for managing our Netscaler MPX5901 (build 12.1).
I’m able to login to the Netscaler but it gives error messages (not authorized to execute this command: show ns license & show ns feature).
When trying to Configuration it gives me; not authorized to execute this command: show ns config).
So basically I cannot do anything.
I assume that there is no command policy linked to the RADIUS user.
But I cannot find any info on how to link a command policy to an external user.
Can you help?
Thanks, Raymond
Did you configure your RADIUS server to send back an attribute with the user’s group membership? Then did you configure the RADIUS Policy on NetScaler to read the attribute from the RADIUS response as AAA groups? Then you can create a AAA group that matches the RADIUS response and bind a cmdpolicy to the AAA group. Here’s sample config – https://support.citrix.com/article/CTX222260
I have two RSA servers, one configured as primary, the other as secondary. I followed your directions for load balancing radius servers. When attempting to add the IP of the RSA vServer, the test connection for radius states it’s states the server is reachable, but either it’s not a valid radius server, or the radius client isn’t configured correctly. I can connect to the radius servers from the NS, and this test passes when communicating directly to the RSA server IP addresses. Any suggestions where I can look?
Is this 11.1? Or 12? If 12, I think you have to add a RADIUS Node with shared secret to the configuration. https://support.citrix.com/article/CTX224302
The problem actually resolved. We were having some issues with RSA servers synchronizing. Once they synced, problem solved. Thanks.
There is no second password field with this setup for users not part of the sms-passcode group. Users that need 2 factor auth, see the username/password field which need to be filled with a domain username/password (i guess also checked by the sms passcode server) after this they get asked for sms passcode in a separte dialog which says “enter passcode” this is how i do it with alle my smspasscode customers.
If SMS can ignore certain users, then it works for me.
Wath do you think of this: 2 auth-policies 1xLDAP (Restriced to a group (LDAP Server definition)) 1xRadius (Restriced to a group in the Radius Software) both bound as primary authentication with the radius having a higher priority (higher number means its prefered in netscaler i found out). Now i can put the user in one of the groups and get the results needed. Which means: User in group “Radius” = (2 factor auth) >>>> User in Group “LDAP” 1 factor auth. works like a charm here. I use SMSPasscode. Do you see any problem in this? Cheers David.
So users that don’t need Radius are told to ignore the second password field?
Dear Carl
i have a use case where some users need 2 factor others only 1 factor authentication on the same Netscaler Gateway (11.1)
How would you set this up?
Cheers David
nFactor, but it only works for web browsers.