Navigation
Workspace app is the new name for Receiver. This post applies to all Workspace app versions, including the Current Release version 2409.10 and the LTSR version 2402 CU3.
- Change Log
- Workspace app versions
- Overview
- Uninstall Old Workspace app Clients
- Installation and Configuration
- Workspace app ADMX GPO Template
- Pass-through Authentication
- Automatically add StoreFront Accounts to Workspace app
- Control Shortcut placement on Desktop and Start Menu – and Workspace Control (Session Reconnect)
- Enable Prelaunch
- Control Device Mapping Prompts
- Desktop Lock
- Use Studio to configure Workspace app Accounts in Published Desktop
- Published Desktop – configure Workspace app to place shortcuts
- Script / Automate Workspace app Self-Service
- Microsoft Teams
- Troubleshoot:
💡 = Recently Updated
Change Log
- 2025 Jan 16 – updated article for Workspace app 2409.10
- 2025 April 2 – Versions – updated for Workspace app 2402 LTSR Cumulative Update 3
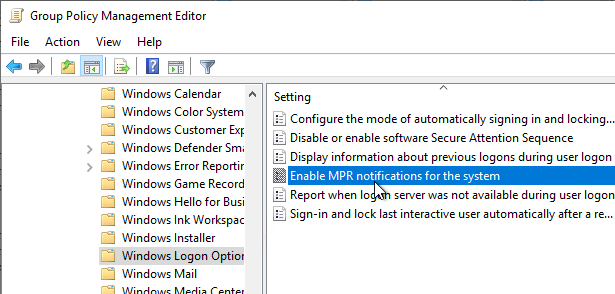
- GPO Settings – SSO in Win11 24H2 requires Enable MPR notifications for the System; Desktop Viewer Toolbar Options
- Registry Values – Remember USB connections
- 2023 Nov 15 – Global App Configuration Service is now available to all on-premises customers even if no Citrix Cloud entitlement.
- 2023 May 4 – Pass-through Authentication – added GPO setting Enable MPR notifications for the System
- 2023 Mar 22 – updated article for Workspace app 2303; anti-dll injection GPO setting
- 2022 Dec 19 – updated article for Workspace app 2212; app protection GPO setting
- 2022 Nov 4 – Versions – updated for Workspace app 1912 LTSR Cumulative Update 7 Hotfix 2
Workspace app Versions
Citrix Workspace app uses a YYMM (year/month) versioning format, of which version 2409.10 (24.9.10.28) is the newest Current Release. See Citrix Docs for the list of new features, some of which only apply to Citrix Cloud.
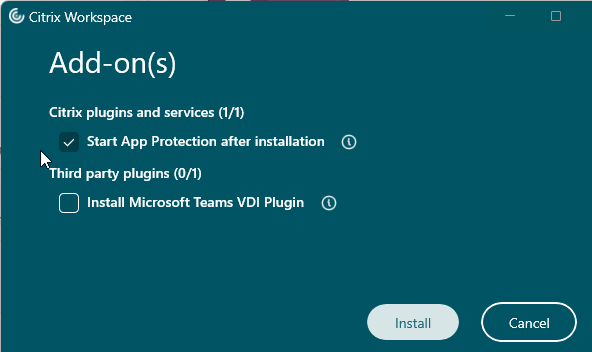
Workspace app 2311 and newer have a new installer interface.

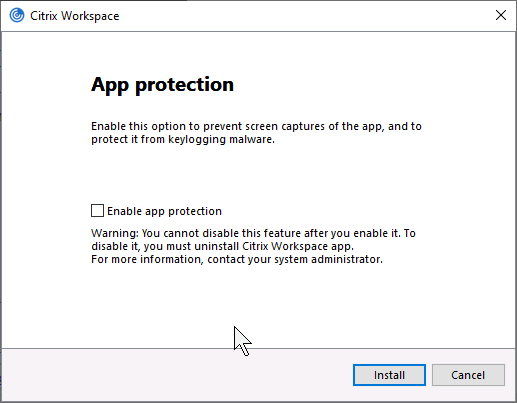
Workspace app 2303 and newer automatically install the App protection components with an option to start them after installation. Older Workspace apps have an option to install App protection and if you don’t select this and later want App protection then you must uninstall Workspace app and reinstall it.
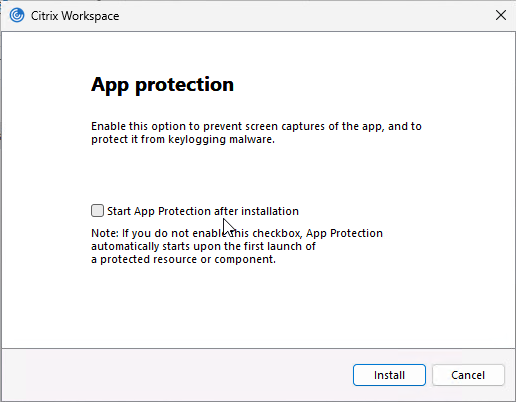
- See App Protection at Citrix Docs to enable App protection for the authentication screen. Workspace app 2305.1 and newer automatically start it for authentication if you have selected the Start App Protection check box during installation.
The newest Current Release version of Workspace app is version 2409.10.
The newest LTSR (Long Term Service Release) version of Workspace app is version 2402 Cumulative Update 3.
Workspace app Modules
The Workspace app installer deploys multiple modules. Here are the important ones:
- ICA Engine (wfica.exe) – process that uses the ICA protocol to connect to published apps and desktops.
- Self-Service (selfservice.exe) – gets icons from StoreFront and displays them in a Window. When an icon is clicked, Self-service passes the ICA file to the ICA Engine to establish a connection.
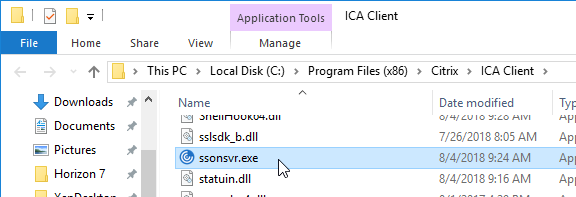
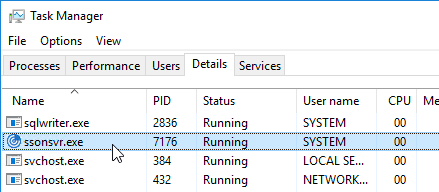
- Single Sign-on (SSON) for ICA (ssonsvr.exe) – captures user credentials and submits them to VDAs after an ICA connection is established
- Workspace Auto-Update (CitrixReceiverUpdater.exe) – Notifies users of Workspace app updates. The most recent name for this component is Citrix Workspace Update.
Custom ICA files are no longer supported. However, Ryan Butler has created a script that asks StoreFront for an ICA file. Explicit credentials are supported. Find the script at Github.
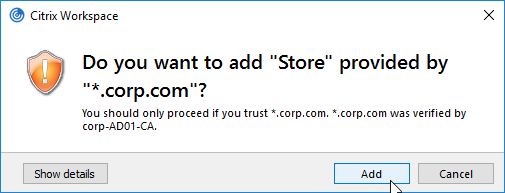
Workspace app Discovery and Beacon Process
If you are using Workspace app’s built-in user interface (instead of a web browser), then Workspace app first prompts you to perform discovery, which is also called Add Account.
Workspace app will contact the FQDN and request download of the StoreFront Provisioning File.
- If you entered a StoreFront FQDN, then Workspace app will download the Provisioning File directly from the StoreFront server.
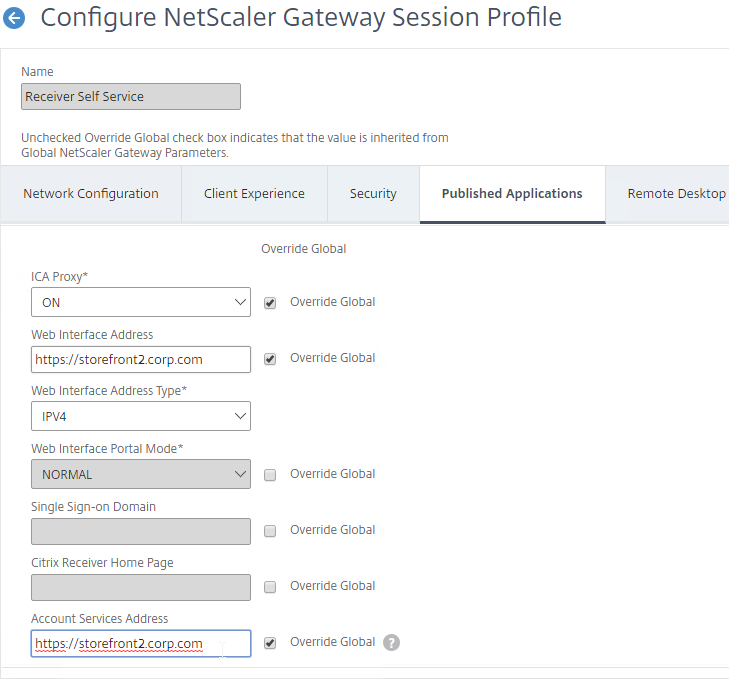
- If you entered a Gateway FQDN, then Gateway will first prompt the user to authenticate. After authentication, Gateway will connect to its configured Account Services address, and download the Provisioning File from StoreFront. The Account Services address is configured in the NetScaler Gateway Session Profile on the Published Applications tab.
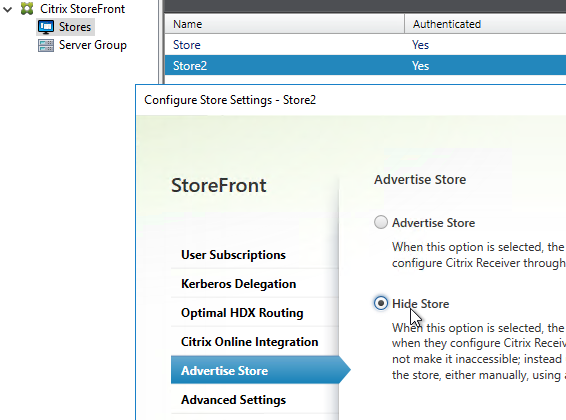
If your StoreFront server is configured with multiple stores, then the user will be prompted to select a store. Unfortunately, there’s no configuration option in NetScaler Gateway to force a particular store.
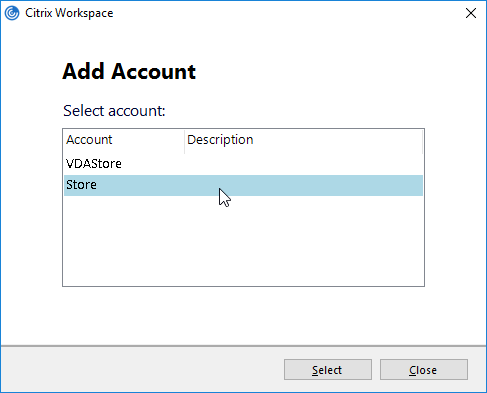
- One workaround is to hide the store that you don’t want visible externally. See How to configure Receiver to a Store that is not advertised for special syntax.
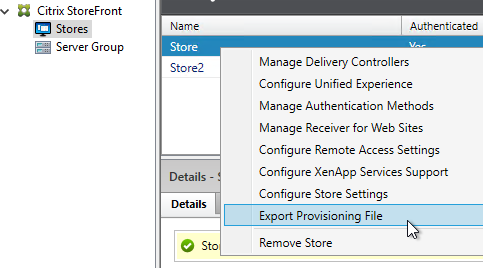
The Provisioning File downloaded from StoreFront is an XML document containing values for several items configured in the StoreFront console. You can export the Provisioning File from the StoreFront console by right-clicking a Store.
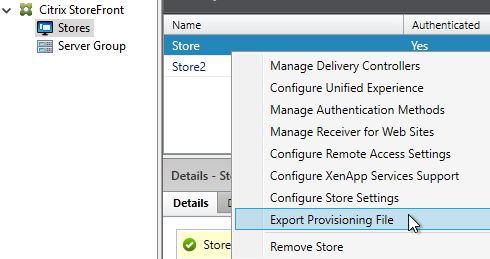
The ReceiverConfig.cr Provisioning File looks something like this:
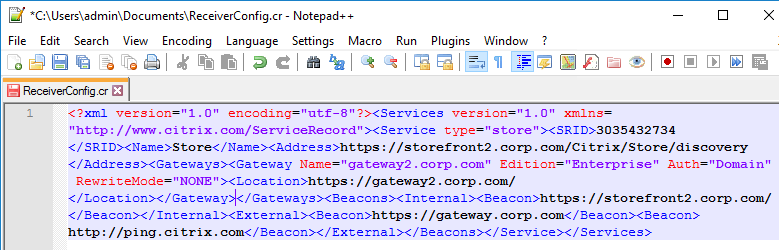
Here are the values in the Provisioning File:
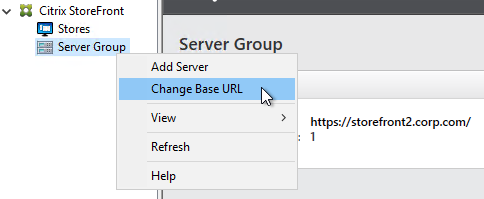
- Address – the Base URL configured in StoreFront Console
- Internal Beacon – as configured in StoreFront Console. This can be the Base URL, or a manually specified URL.
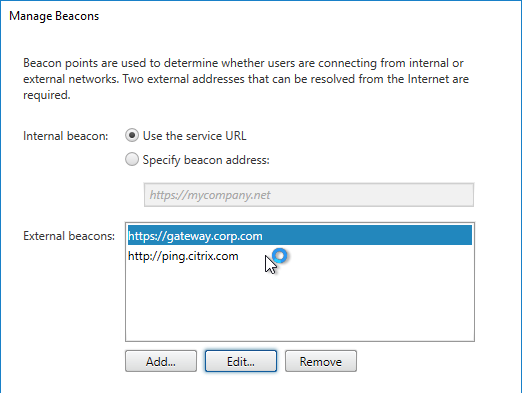
- External Beacons – as configured in StoreFront Console
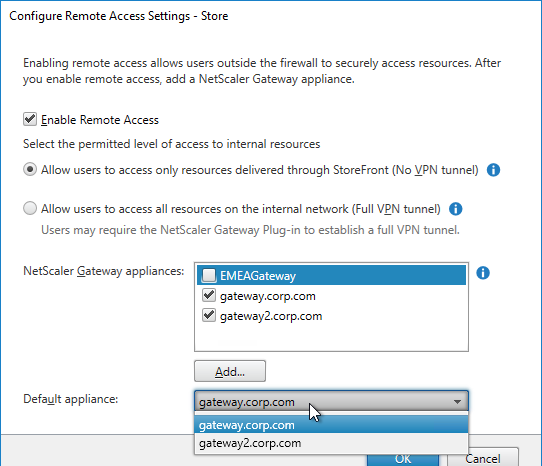
- Gateways – as configured in StoreFront Console. If there are multiple Gateways, when enabling Remote Access on the Store, then only one Gateway is selected as Default
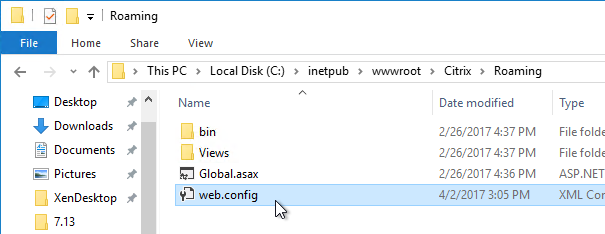
- SRID – Store ID. An important value to consider for multi-datacenter configurations. The SRID is set when the Store is created. It can also be changed by editing C:\inetpub\wwwroot\Citrix\Roaming\web.config.
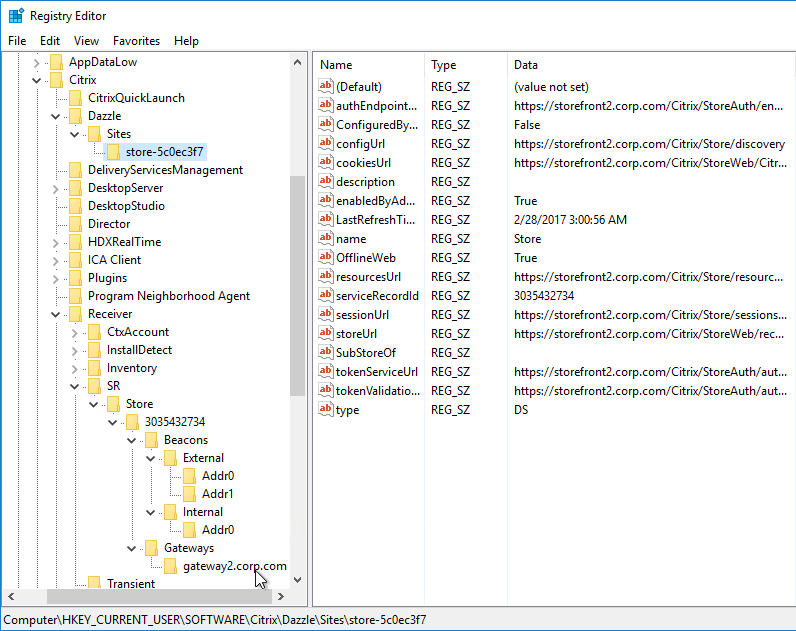
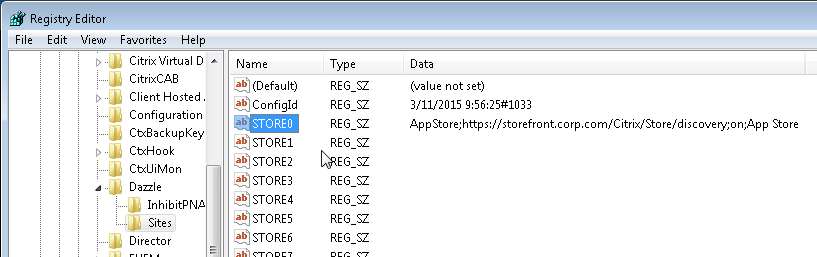
Workspace app reads the Provisioning File, and configures itself by inserting the file’s contents into the user’s registry. The values are located under HKCU\Software\Citrix\Dazzle\Sites and HKCU\Software\Citrix\Receiver\SR. If you performed discovery through NetScaler Gateway, notice that the internal Base URL is added to the user’s registry.
Once Workspace app is configured, it then performs the following steps:
- Attempt to connect to the Internal Beacon.
- If the Internal Beacon is reachable, connect directly to the StoreFront Base URL (Address).
- If the Internal Beacon is not reachable:
- Attempt to connect to the External Beacons. If the External Beacons are not reachable, then stop attempting to connect.
- Connect to the Gateway address configured in the Provisioning File. If there is more than one Gateway, connect to the Gateway that is marked as the Default.
Here are some interesting notes on this connection process:
- The FQDN you entered during Discovery has absolutely nothing to do with how Workspace app connects to StoreFront or Gateway. The actual connection process is controlled by the contents of the Provisioning File, not the Discovery address.
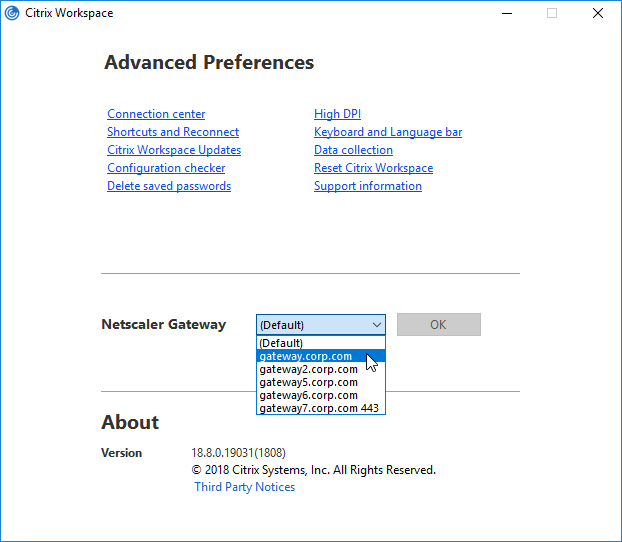
- If the Provisioning File has multiple Gateways defined, Workspace app uses whichever Gateway is marked as Default. Workspace app completely ignores whatever Gateway FQDN you entered during Discovery. To use a non-default Gateway, the user must manually select the other Gateway in Workspace app’s Advanced Preferences.
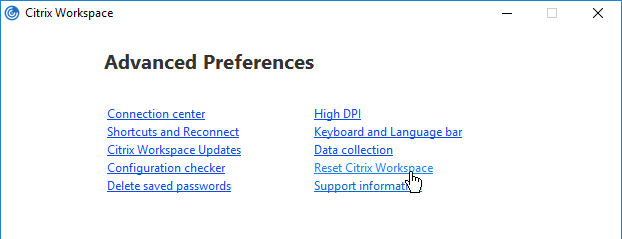
In StoreFront Console, if any configuration changes are performed that affect the Provisioning File, it takes an hour for Workspace apps to reconfigure themselves automatically. Or users can remove Accounts and re-add (or Reset Citrix Workspace) so that the updated Provisioning File is imported.
Here are some additional methods of performing Workspace app Discovery:
- After exporting the Provisioning File from StoreFront Console, distribute it to users, and ask them to double-click it.
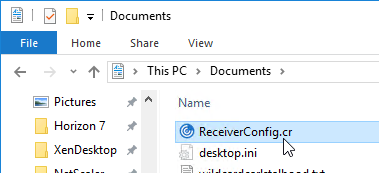
- After logging in to Receiver for Web (StoreFront), at the top right, click the username, and click Activate. This downloads the receiverconfig.cr file, which is identical to the one you can export from StoreFront Console. The user then must run the downloaded file.
Virtual Monitors
In Workspace app 1812 and newer, when connected to a published desktop on a single monitor, you can split the screen into virtual monitors. This feature is intended for large 4K monitors.
- In the desktop toolbar at the top of the screen, click Preferences.
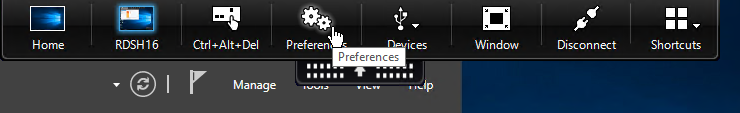
- Switch to the Monitor Layout tab.
- On the bottom, select Horizontal or Vertical, then click somewhere in the blue box to draw a line. The single monitor will be split along this line. You can set different DPI for each portion of the virtual display.
- Right-clicking one of the split sections changes that section to the primary display.
- Click OK when done.
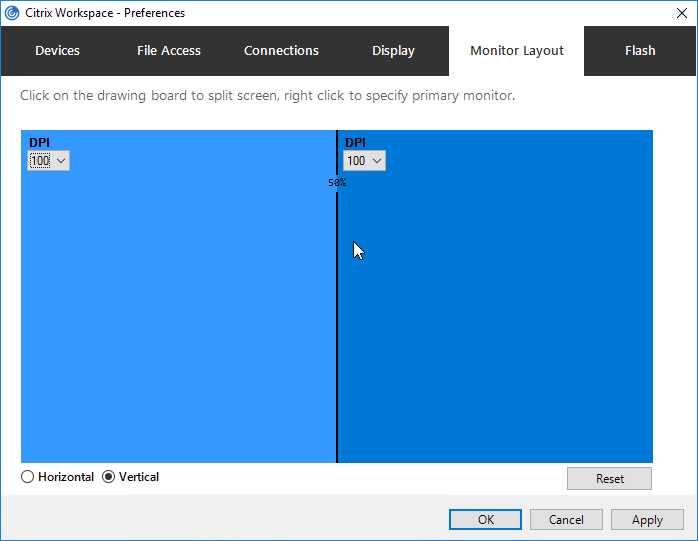
- In the toolbar, click Window to resize it to a window, and then click Full Screen to cause your virtual monitor configuration to take effect.
Uninstall Old Clients
Workspace app installer can do a force uninstall of old clients before installing the new version:
- In Workspace app 2309 and newer, run CitrixWorkspaceApp.exe /CleanInstall /Silent
- In Workspace app 1909 and newer, run CitrixWorkspaceApp.exe /ForceInstall /Silent.
- In Workspace app 1908 and older (including Receiver), run CitrixWorkspaceApp.exe /RCU /Silent or CitrixReceiver.exe /RCU /Silent.
Citrix CTX325140: How to Remove Client Files Remaining on System after Uninstalling Receiver for Windows.
Installation and Configuration
Administrator privileges – Administrator privileges are required to install any missing prerequisites.
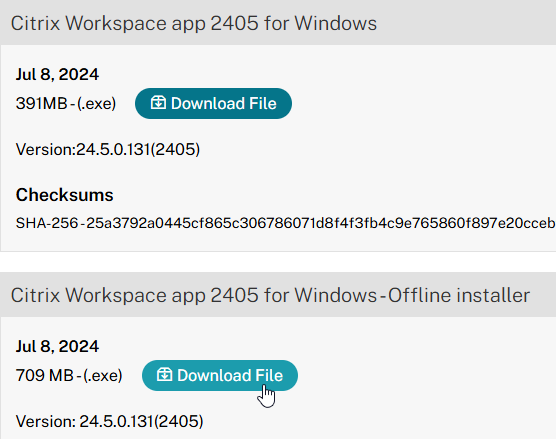
Internet required – Recent versions of Workspace app download and install Microsoft Edge WebView2 Runtime, .NET Desktop Runtime 6.0.20, .NET Framework 4.8, and Visual C++. Internet access is required for the Workspace app installer to download these install files. Or there’s an Offline Installer for Workspace app 2309 and newer.
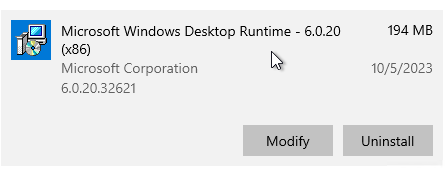
.NET Desktop Runtime 6.0.20 – Workspace app 2309 and newer will install x86 .NET Desktop Runtime 6.0.20 if it’s not already installed.
This section contains a summary of all common command line switches, registry keys, and policy settings for Workspace app.
Links:
- Citrix Blog Post: Optimizing Citrix Receiver for Pre-launch and Single Sign-On
- Citrix CTX202002 How To Deploy Citrix Receiver for Windows Using SCCM 2012 R2
Workspace app 2203 LTSR CU2 and Workspace app 2212 and newer fix security vulnerabilities.
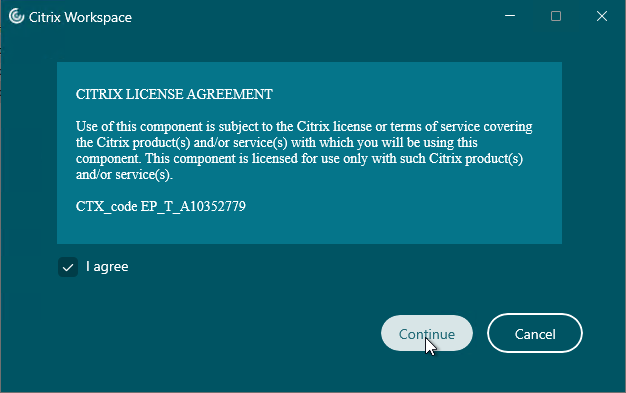
CitrixWorkspaceApp.exe current release version 2409.10 or LTSR version 2402 CU3 can be installed by simply double-clicking it.
- LTSR Workspace app does not support Browser Content Redirection.
- Workspace app 2006 and newer do not support Windows 7.
- Workspace app 2206 and newer enable DPI Matching by default. DPI Matching can be disabled through client-side group policy, or in the Advanced Preferences in Workspace app 2212 and newer. DPI Matching prevents connections to CVAD 7.15. Multi-session VDAs with version 1912, by default, have DPI Matching disabled, but can be enabled in the VDA’s registry. See CTX460068 for details.
- Workspace app 2311 and newer have a new interface for installation.

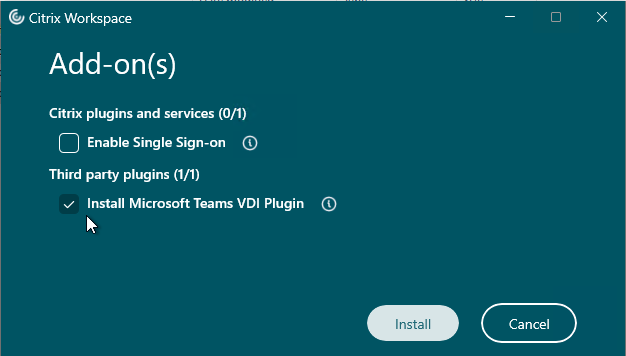
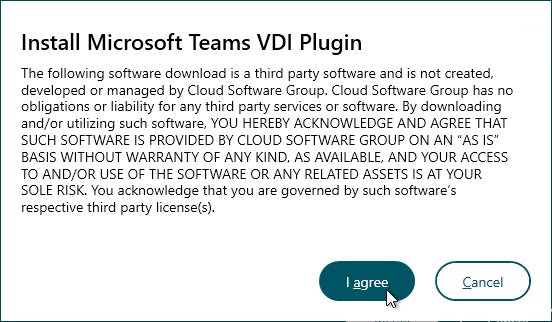
- Workspace app 2402 and newer ask if you want to install the Microsoft Teams VDI Plugin or not. This is for Teams 2.1 and newer.
Administrator vs non-administrator
- Non-administrator – If a non-administrator installs Workspace app, then each non-administrator that logs in to the same workstation will have to reinstall Workspace app.
- Non-administrator installations are installed to %USERPROFILE%\AppData\Local\Citrix\ICA Client for each user.
- Administrator – If CitrixWorkspaceApp.exe is installed using an administrator account. then the Workspace app only needs to be installed once.
- Administrator installations are installed to C:\Program Files (x86)\Citrix\ICA Client.
- Administrator installations of Workspace app 1912 and newer can be manually upgraded by non-administrators by clicking Check for Updates. Older versions cannot be upgraded by non-administrators.
- Conflicts – If an administrator install of Workspace app is performed on a machine that has non-administrator installs of Workspace app, then the two installations will conflict. Best option is to uninstall non-admin Workspace app and Receiver before installing admin Workspace app. Otherwise, the user’s profile probably has to be reset before Workspace app is functional again.
- Citrix article CTX249920 Workspace App for Windows – Your apps are not available at this time – Issue when installing Citrix Receiver in not elevated/per-user install mode describes the HKEY_CURRENT_USER registry keys that must be deleted to fix this issue.
- For a script to clean-up the per-user installs, see Mark DePalma at Citrix Receiver Per-User Install Cleanup.
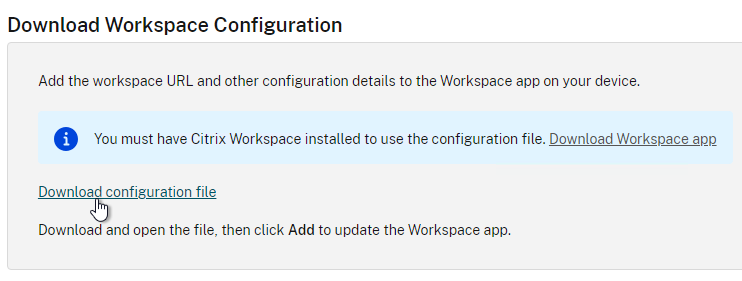
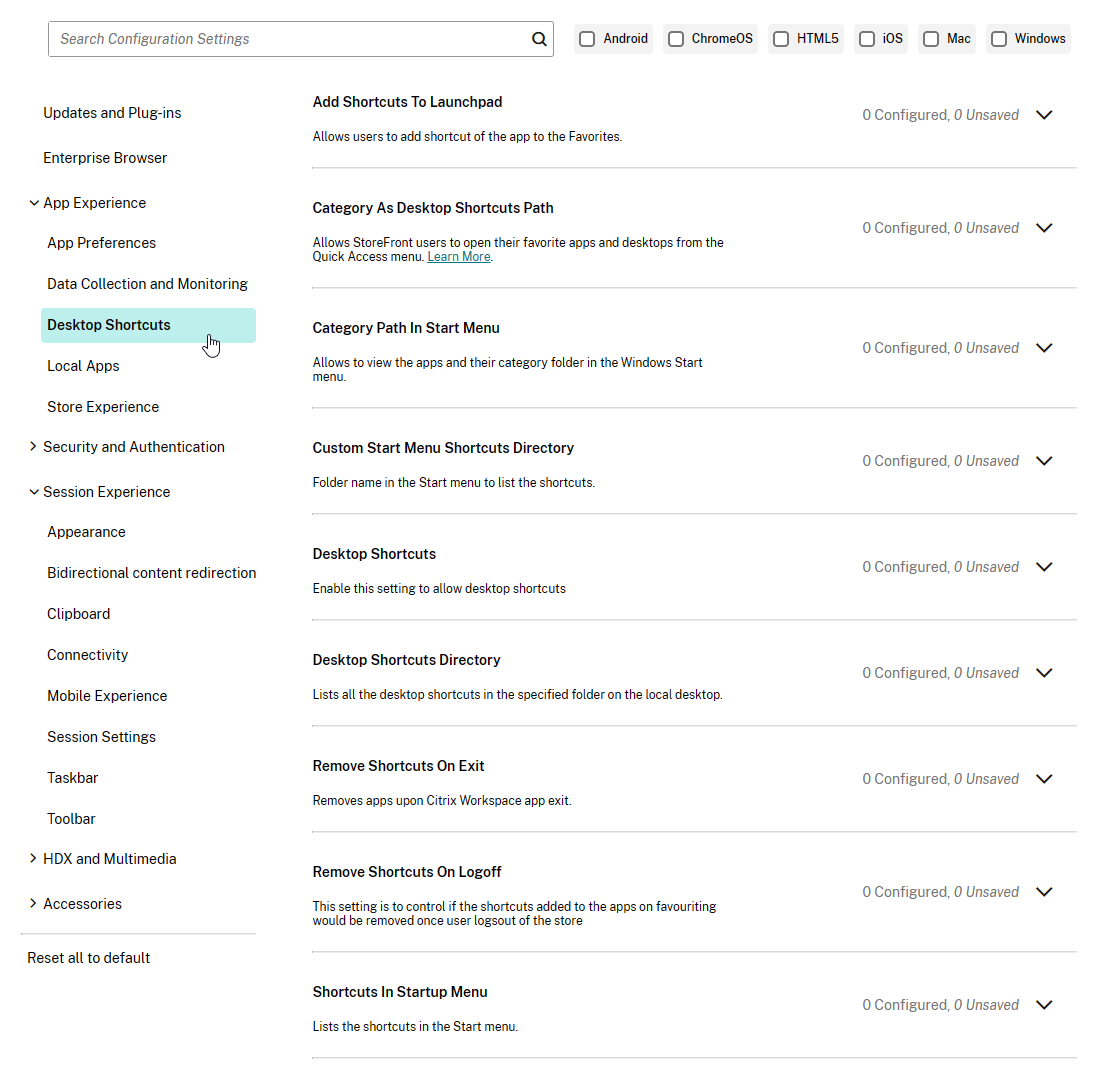
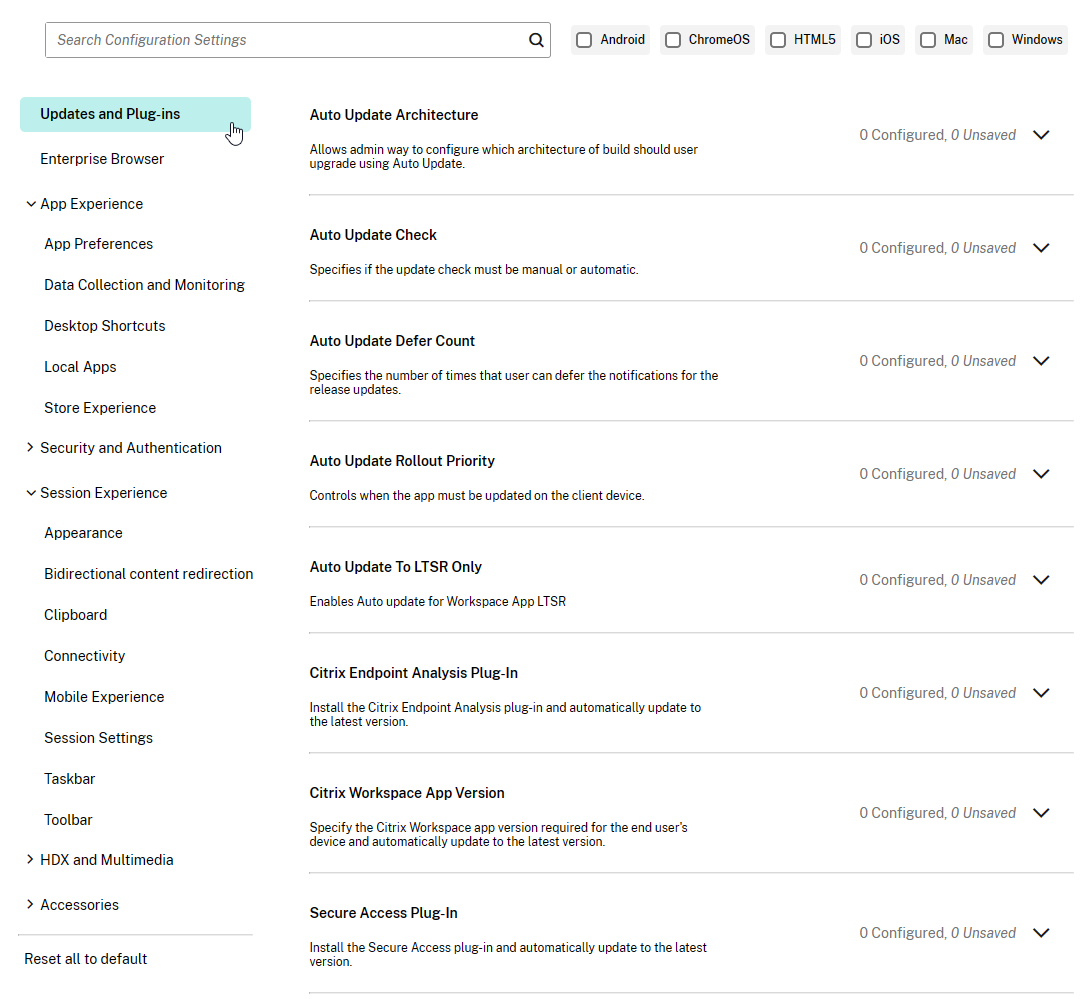
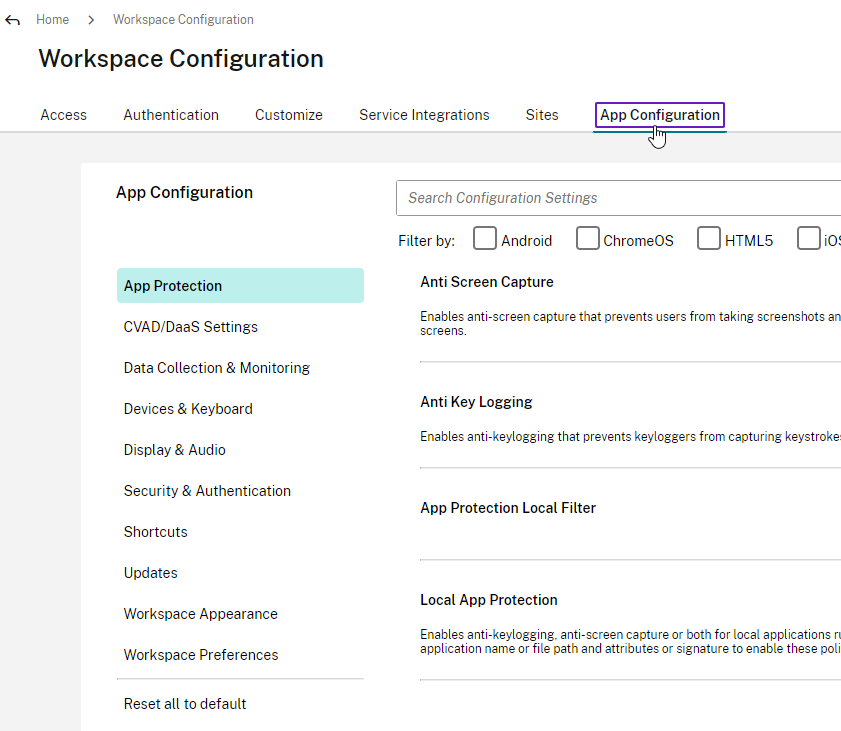
Global App Configuration Service
Global App Configuration Service (GACS) is a Citrix Cloud service that can push configurations to Workspace app clients. This Citrix Cloud service is now available to all on-premises customers even if you don’t own any Citrix Cloud entitlements.
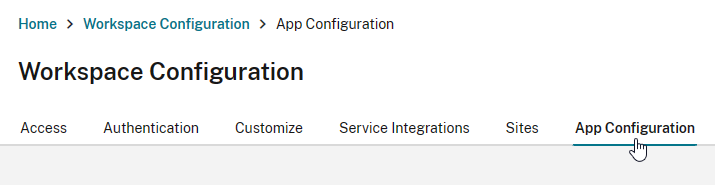
- Login to https://citrix.cloud.com. If you don’t have a Citrix Cloud account, then login using your Citrix.com account credentials and it will create a Citrix Cloud account.
- Use the top left hamburger menu to go to Workspace Configuration.
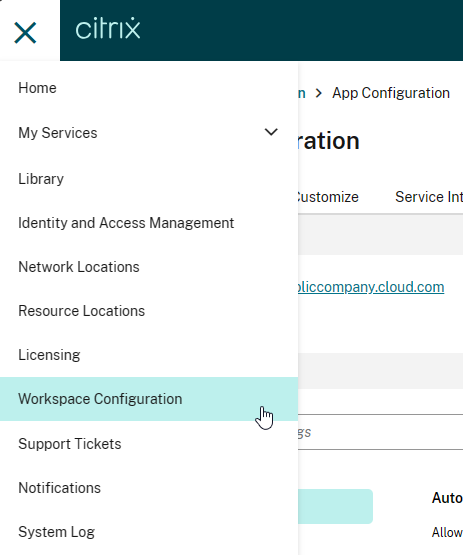
- Switch to the tab named App Configuration.
- Click Switch URL.
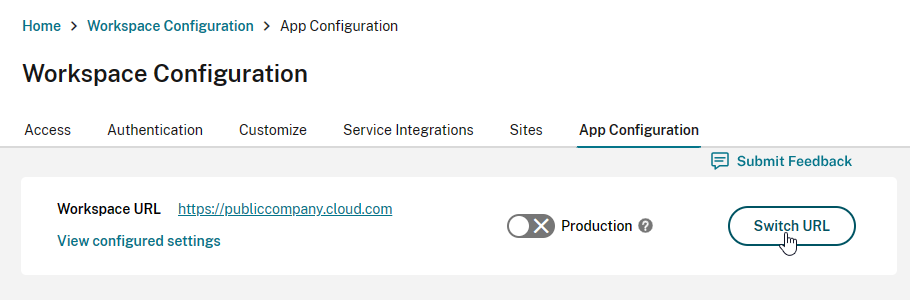
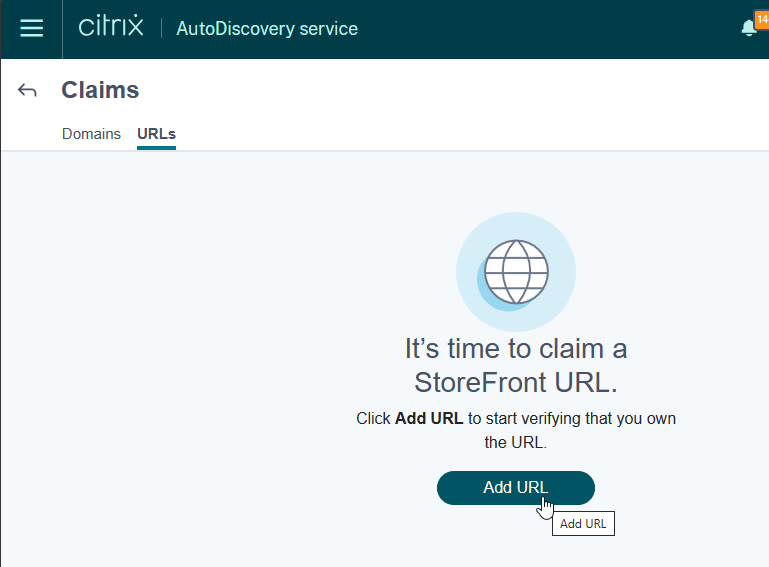
- Near the bottom, click Claim URL.
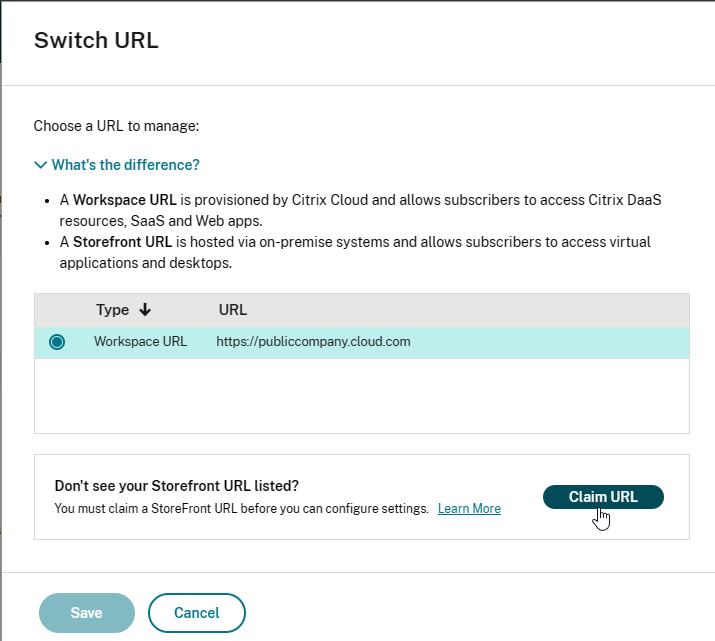
- Click Add URL to add your on-premises StoreFront/Gateway URL. See Citrix Docs for details. GACS uses this URL to determine which Workspace app clients should receive the settings that you configure.
- Back in the App Configuration page, you can now configure Workspace app settings as desired. Workspace apps that have stores under the claimed URL will then receive these settings.
Auto-Update
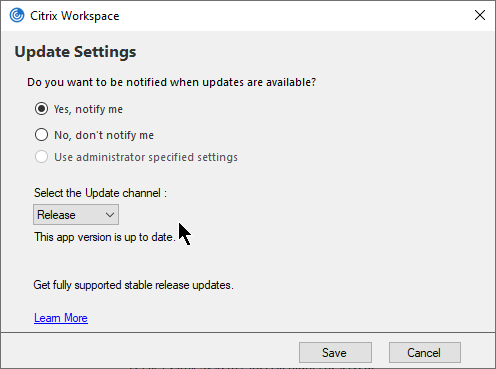
Workspace app supports auto-update.
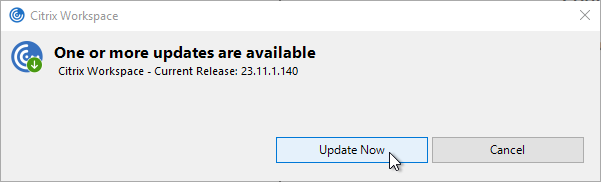
Some notes:
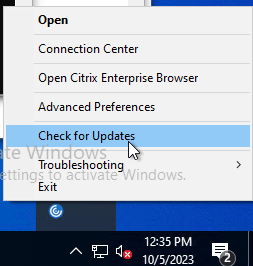
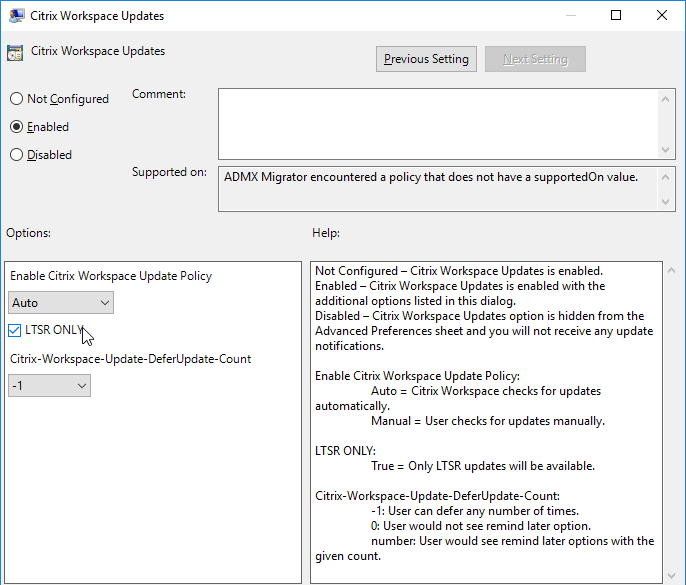
- If Workspace app 1912 or newer is installed as administrator, then non-administrators can click Check for Updates to manually update Workspace app. To prevent this, use group policy to disable Citrix Workspace Updates.
- Older versions of Workspace app cannot be upgraded by non-administrators.
- If Workspace app is installed on a VDA, auto-update is automatically disabled. This includes Remote PC.
- Auto-update can be limited to LTSR updates only.
- Auto-update is configurable through several mechanisms: group policy, StoreFront, Workspace app GUI, installer command line. See Configuring Citrix Workspace Updates at Citrix Docs.
- Workspace app 2107 and later let users select an Update channel.
- See George Spiers Citrix Receiver for Windows Auto-Update.
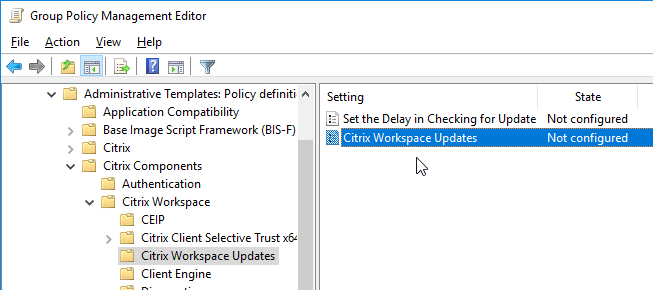
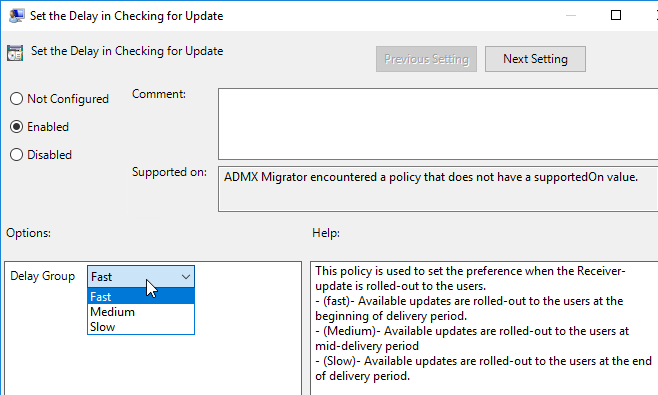
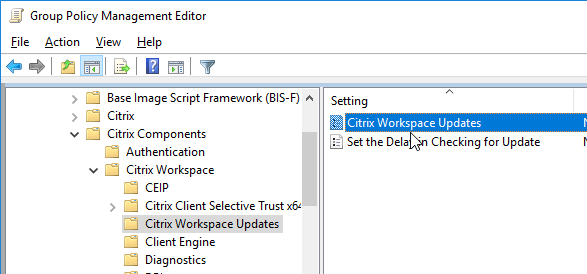
Auto-update is configured using Workspace app group policy under the Citrix Workspace Updates, or Auto-Update node.
Or use Global App Configuration Service.
Workspace app Splash Screen
Workspace app shows a Splash Screen on first launch with the text “Citrix Workspace app extends the capabilities of Citrix Receiver”.
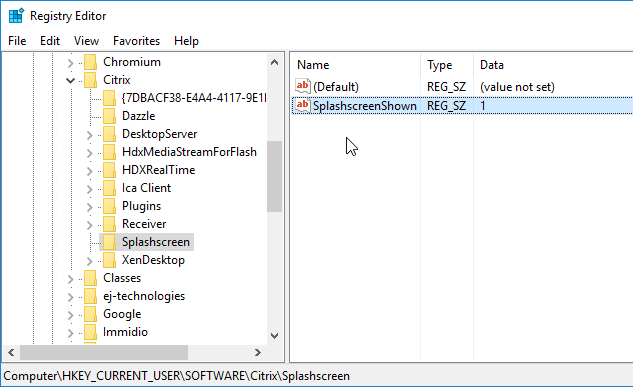
To prevent this splash screen, set the following registry value: (source = Dennis Span on Twitter)
- Key = HKEY_CURRENT_USER\SOFTWARE\Citrix\Splashscreen
- Value (REG_SZ) = SplashscreenShown = 1
Add Account Wizard
After installation, Workspace app will launch and ask you to add an account. If Workspace app, notice the checkbox Do not show this window automatically at logon.
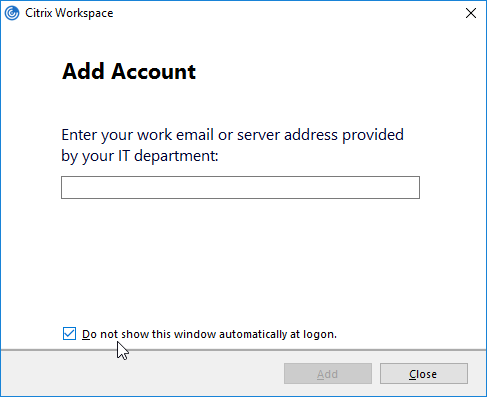
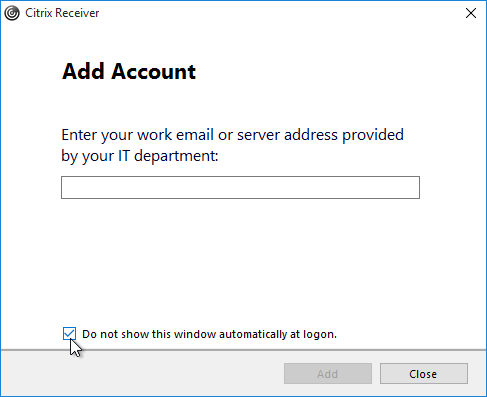
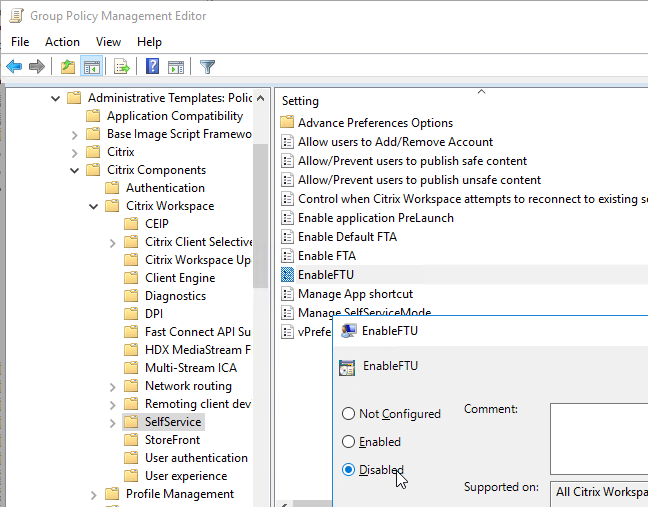
FTU (First Time Use aka Add Account Wizard) will be displayed only if a store is not configured. If a store is already configured via command line, GPO, or Citrix Studio, then FTU screen will not be available after installation. Otherwise, FTU can be suppressed by doing one of the following:
- Rename CitrixWorkspaceApp.exe to CitrixWorkspaceAppWeb.exe.
- Install using a command line switch:
- CitrixWorkspaceApp.exe /ALLOWADDSTORE=N
- Set the registry value: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Citrix\EnableFTU=dword:00000000 (or EnableX1FTU =dword:0)
- Disable the EnableFTU policy setting in Receiver.admx.
- Change Registry values post installation to suppress the Add Account window. Under HKLM\Software\Wow6432Node\Citrix\Dazzle, set AllowAddStore value to N.
- Set the registry value: HKEY_LOCAL_MACHINE\Software\Citrix\Receiver\NeverShowConfigurationWizard (REG_SZ) = true
- Also see Suppressing Add Account dialog at Citrix Docs.
Discover Hidden Stores
When Workspace app is first launched, it must perform Discovery, which is the process of downloading the .xml provisioning file from StoreFront. Discovery is performed by entering a StoreFront FQDN or Gateway FQDN. To discover a hidden store (a store that’s not advertised), add ?StoreName to the end of the FQDN. CTX214819 How to configure Receiver to a Store that is not advertised.
CitrixWorkspaceApp.exe Command line switches
CTX227370 Citrix Workspace app Commandline Tool contains a GUI tool to build your installer command line.

For unattended installation of Workspace app, see CTA Dennis Span Citrix Workspace App unattended installation with PowerShell or Citrix Receiver unattended installation with PowerShell.
Installer Command Line Switches are detailed at Configure and install Receiver for Windows using command-line parameters at Citrix Docs. Common Command line switches include the following:
- /silent
- /includeSSON – enables pass-through authentication. GPO configuration is also required as detailed below.
CitrixWorkspaceApp.exe /includeSSON
- /ALLOWADDSTORE=A – by default, only SSL (HTTPS) stores are accepted. To allow non-SSL stores:
CitrixWorkspaceApp.exe /ALLOWADDSTORE=A
- /STORE0 – To add a store from the installation command line:
CitrixWorkspaceApp.exe STORE0="AppStore;https://Citrix.corp.com/Citrix/MyStore/discovery;on;App Store"
- Workspace App can discover the Store through NetScaler Gateway.
CitrixWorkspaceApp.exe STORE0="AppStore;https://gateway.corp.com#MyStore;On;App Store"
- Workspace App can discover the Store through NetScaler Gateway.
- /SELFSERVICEMODE=False – disables the Self-Service interface and enables shortcut-only mode:
CitrixWorkspaceApp.exe /SELFSERVICEMODE=False
- /AutoUpdateCheck=auto /AutoUpdateStream=LTSR – enables Citrix Workspace Update notifications and sets it to LTSR Branch only. AutoUpdateCheck can also be set to manual or disabled. AutoUpdateStream can also be set to Current. See Configuring Citrix Workspace Updates at Citrix Docs.
CitrixWorkspaceApp.exe /AutoUpdateCheck=auto /AutoUpdateStream=LTSR
- /ENABLEPRELAUNCH=True – enables prelaunch:
CitrixWorkspaceApp.exe /ENABLEPRELAUNCH=True
- /ALLOW_CLIENTHOSTEDAPPSURL=1 – enables Local App Access:
CitrixWorkspaceApp.exe /ALLOW_CLIENTHOSTEDAPPSURL=1
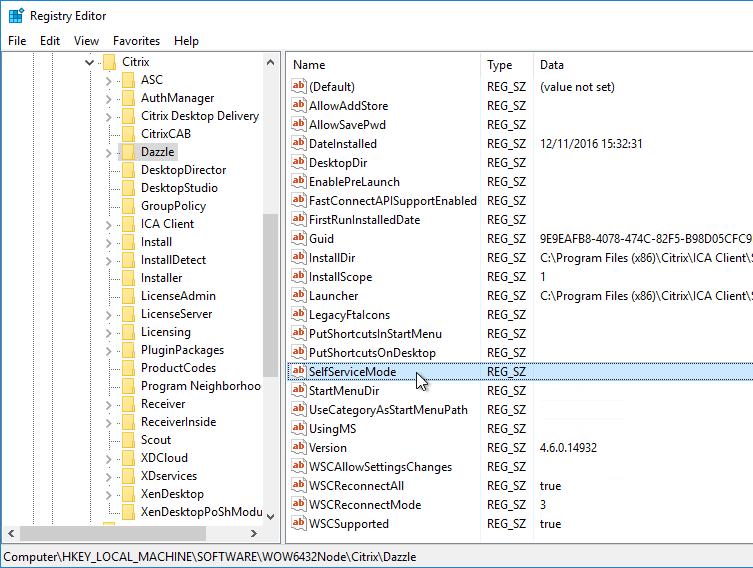
Registry values
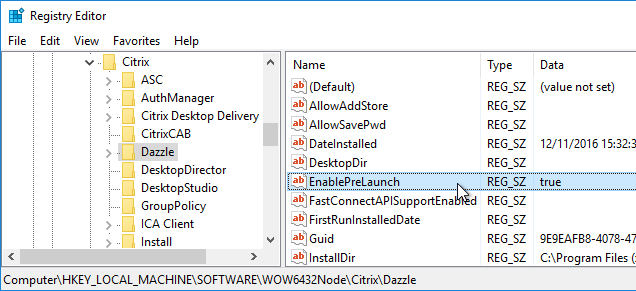
HKLM\Software\Wow6432Node\Citrix\Dazzle on the Workspace app machine. All are of type REG_SZ (string) unless specified. Note: several of these are configurable using the Reciever.admx group policy template.
- SelfServiceMode (REG_SZ) = False – Turns off Workspace app’s Self-Service interface.
- PutShortcutsOnDesktop (REG_SZ) = True – If Self-Service interface is disabled, places all shortcuts on desktop.
- UseDifferentPathsforStartmenuAndDesktop (REG_SZ) = True
- UseCategoryAsStartMenuPath (REG_SZ) = True or False
- UseCategoryAsDesktopPath (REG_SZ) = True or False
- StartMenuDir (REG_SZ) = name of folder on Start Menu where shortcuts are placed.
- DesktopDir (REG_SZ) = name of folder on Desktop where shortcuts are placed
- EnablePreLaunch (REG_SZ) = True – If SSON is enabled then PreLaunch is already enabled by default.
- AllowAddStore (REG_SZ) = A – Only if using http (instead of https) to connect to StoreFront.
- AllowSavePwd (REG_SZ) = A – Only if using http (instead of https) to connect to StoreFront.
- UserDomainName (REG_SZ) = pre-filled domain name
- InitialRefreshMinMs (REG_SZ) = 1 – minimizes the launch delay before contacting store
- InitialRefreshMaxMs (REG_SZ) = 1 – minimizes the launch delay before contacting store
- RefreshMs (REG_SZ) = 3600000 (1 hour) – interval for Receiver icon refreshes. 1 hour is the default value.
- RefreshMs (REG_SZ) = 18000000 – Citrix CTX213755 Citrix Receiver Shows Authentication Window Periodically When Receiver is Not Opened
- MaxSimultaneousFetches (REG_DWORD) = 6 – improves the time of loading icons in Start Menu
- MaxSimultaneousSubscribes (REG_DWORD) = 6 – improves the time of loading icons in Start Menu
- DontWarnOfRemovedResources (REG_SZ) = True – prevents dialog boxes when resources are removed from the server. (or False)
- SilentlyUninstallRemovedResources (REG_SZ) = True – prevents dialog boxes when resources are removed from the server
- PreferTemplateDirectory (REG_SZ) = UNC path or local path containing shortcuts copied by the prefer keyword. Give the shortcuts a short name.
- PnaSSONEnabled (REG_SZ) = True – Enables Single Sign-on for PNAgent (Web Interface).
- WSCReconnectMode (REG_SZ) = 3 (default) – If this Workspace app is running inside a VDA published desktop, set it to 0.
- If you’re having trouble getting sessions to reconnect, see Receiver 4.3 Desktop will not auto-reconnect when logging into a machine at Citrix Discussions
- AlwaysUseStubs (REG_SZ) = True. Workspace app and Receiver 4.3.100 and newer don’t create .exe stubs by default. Set this to create .exe stubs. Also see Citrix CTX211893 Controlling Shortcut behavior in Receiver 4.3.100.
- DontCreateAddRemoveEntry (REG_SZ) = True – don’t create “Delivered by Citrix” entries in Programs and Features
- DesktopNameFormatString = format string for shortcut names – For example “{0}_{1}_{2}_{3}”. See the link for details.
- SelfServiceFlags (REG_DWORD) = 4 – prevents duplicate shortcuts when roaming and Desktop is redirected.
- SelfServiceFlags = 5 to stop external SSON from prompting for authentication
- ReEvaluateNetwork (REG_SZ) = true – for Beacon detection with Single FQDN
To prevent the Win+G popup on Windows 10 machines:
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\GameDVR
- AllowGameDVR (REG_DWORD) = 0
To allow adding non-HTTPS stores to Workspace app:
- HKLM\Software\Wow6432Node\Citrix\AuthManager
- ConnectionSecurityMode (REG_SZ) = Any
To increase ICA bandwidth consumption over high latency links, set:
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\ICA Client\Engine\Configuration\Advanced\Modules\TCP/IP
- OutBufCountClient2 = Number of OutBufs (default is 44)
- OutBufCountHost2 = Number of OutBufs (default is 44)
- See CTX125027 How to Optimize HDX Bandwidth Over High Latency Connections for some recommended values (multiples of 44)
To prevent beacon probing from using proxy, set:
- HKEY_LOCAL_MACHINE\Software\WOW6432Node\Citrix\Receiver\inventory
- BeaconProxyEnabled (REG_DWORD) = 0
To enable foreground progress bar, set:
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\ICA Client
- ForegroundProgressBar (REG_DWORD) = 1
For client-to-server file type redirection, set:
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\ICA Client\Engine\Configuration\Advanced\Modules\ClientDrive
- NativeDriveMapping=”TRUE”
To fix USB devices that emulate a keyboard, set:
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\ICA Client\Engine\Lockdown Profiles\All Regions\Lockdown\Virtual Channels\Keyboard
- KeyboardTimer=”10”
To remember manually mapped USB devices when auto-connection is enabled, set: (2409 and newer)
- HKLM\SOFTWARE\Citrix\ICA Client\GenericUSB (same path for 32-bit and 64-bit, create the keys)
- RememberConnections (DWORD) = 0x1
To override the devices that are mapped using optimized channels instead of generic USB, see Citrix CTX123015 How to Configure Automatic Redirection of USB Devices
Group Policy Settings
Copy the Workspace app ADMX template (C:\Program Files (x86)\Citrix\ICA Client\Configuration\receiver.admx) to C:\Windows\PolicyDefinitions (or Sysvol). Also copy receiver.adml to C:\Windows\PolicyDefinitions\en-us (or Sysvol).
Edit a GPO that applies to client machines, go to Computer Configuration | Policies | Administrative Templates | Citrix Components | Citrix Workspace and configure the following:
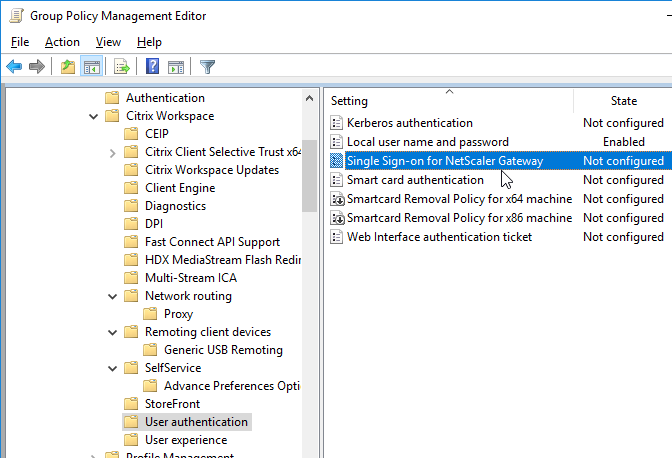
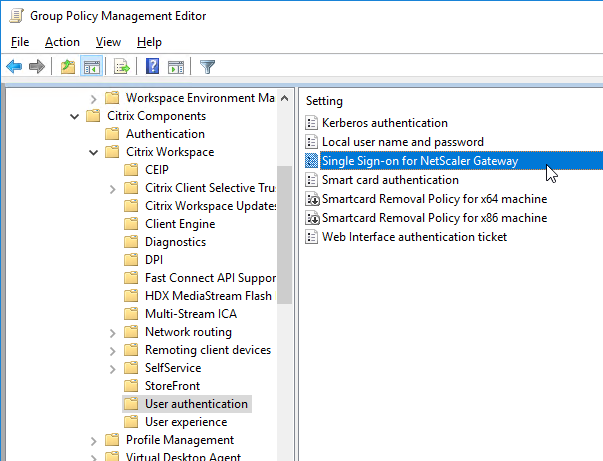
- To enable pass-through authentication: go to | User Authentication |.
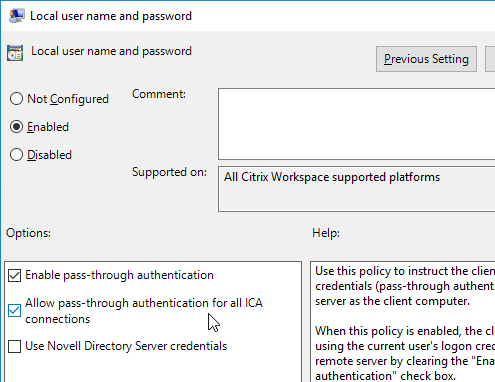
- Local Username and Password – Check the top two boxes.
- Also add the StoreFront FQDN to the Local Intranet zone in Internet Explorer.
- Single Sign-on for NetScaler Gateway (Workspace app 1808 and newer)
- To add a store, go to | StoreFront |
- StoreFront Accounts List – see the help text
- To enable Auto-Update, go to | AutoUpdate | or | Citrix Workspace Updates |. (the node was renamed in 4.11 and Workspace app)
- Enable or Disable AutoUpdate or
- Citrix Workspace Updates
- To modify the desktop viewer toolbar, go to | Client Engine |
- Desktop Viewer Toolbar Options (2409 and newer)
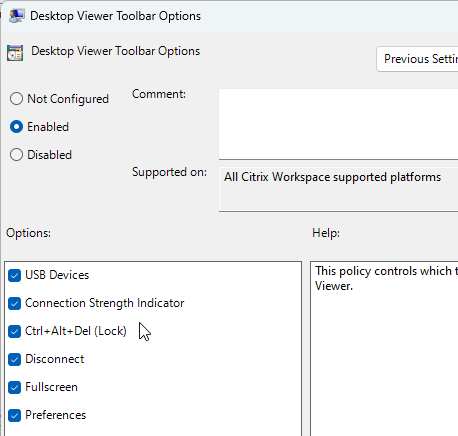
- Desktop Viewer Toolbar Options (2409 and newer)
- To enable Local App Access, go to | User Experience |
- Local App Access Settings
- To prevent the endpoint from sleeping while session is active, go to | User Experience |
- Power Management (2405 and newer)
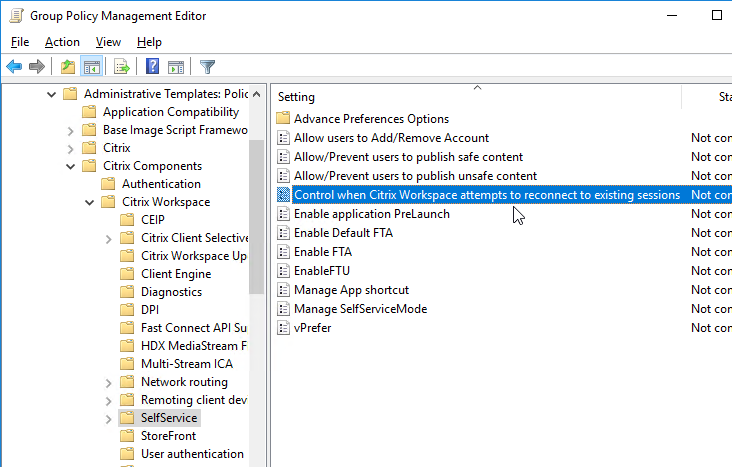
- To configure the Self-Service interface, go to | SelfService |
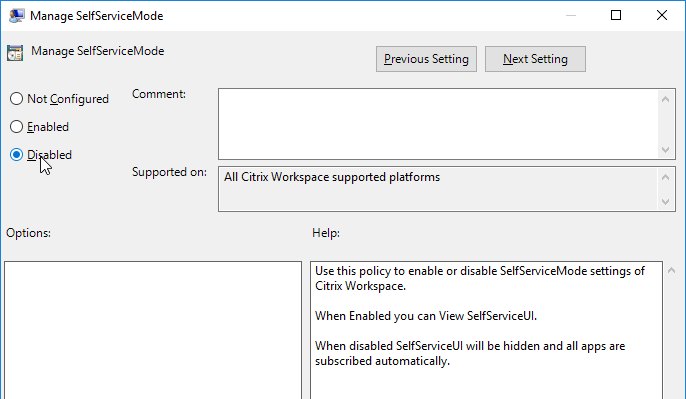
- Set Manage SelfServiceMode to Disabled to completely disable the Self-Service window. This causes all icons to be placed on the Start Menu.
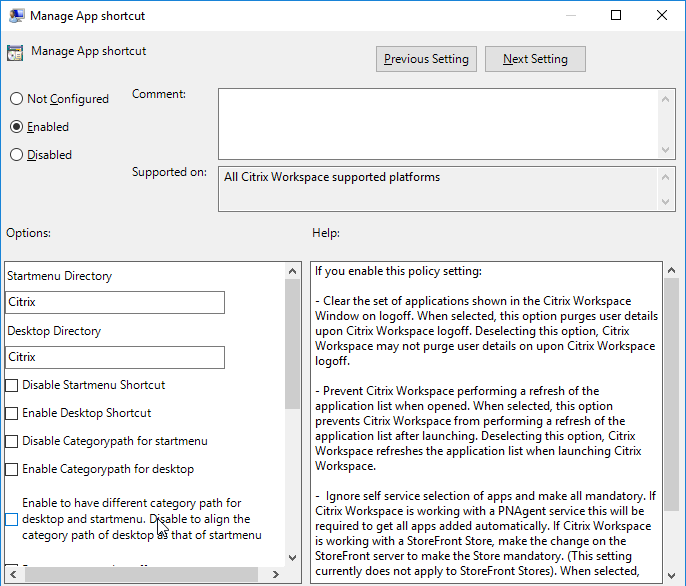
- Enable Manage App Shortcut and configure it as desired.
- To allow the Self-Service window, but prevent it from automatically opening (reside in systray), tick Prevent Citrix Workspace performing a refresh of the application list when opened. Source
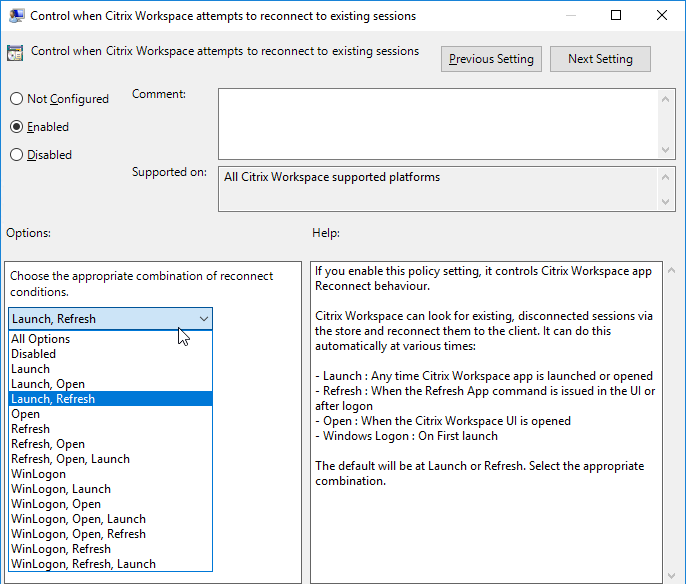
- Enable Control when Workspace attempts to reconnect to existing sessions. If this is a VDA published desktop, set it to Disabled. Otherwise configure it as desired.
- Set Enable FTU to Disabled to prevent the Add Account wizard from displaying.
- Enable Allow/Prevent users to publish unsafe content if publishing content that’s opens a file or file share.
Enable automatic client drive and client microphone mapping:
- In a client-side GPO, add the GPO ADM template from http://support.citrix.com/article/CTX133565.
- Enable the setting Create Client Selective Trust Keys. See Below for details.
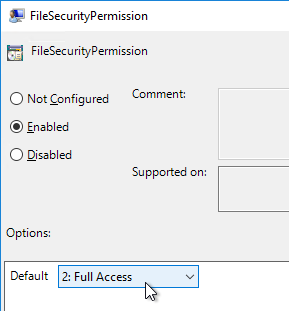
- Configure the FileSecurityPermission setting in one or more of the regions.
- Configure the MicrophoneAndWebcamSecurityPermission setting in one or more of the regions.
Citrix CTX203658 Start Menu Icons Set to Default (Blank Document) After Update to Receiver 4.3.100 – Windows 8 and newer
- Computer Configuration | Policies | Administrative Templates | Windows Components | File Explorer
- Allow the use of remote paths in file shortcut icons = enabled
For Single Sign-on in Windows 11 24H2 and newer, enable the following GPO setting:
- Computer Configuration | Policies | Administrative Templates | Windows Components | Windows Logon Options
- Enable MPR notifications for the System = enabled
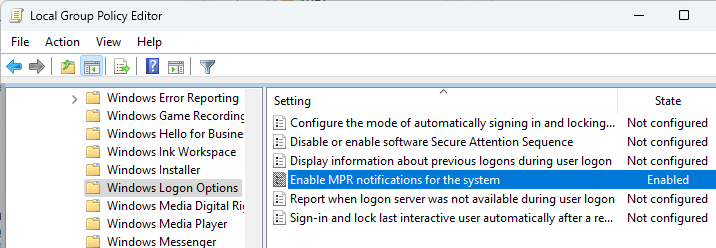
- Enable MPR notifications for the System = enabled
Deploy Workspace app using Active Directory
To deploy Workspace app using Active Directory, configure a GPO with a computer startup script that runs the Workspace app installer executable. Citrix provides sample scripts that can be downloaded from one of the Workspace app download pages (Workspace app current release version 2409.10, or LTSR version 2402 CU3, by expanding Downloads for Admins (Deployment Tools).
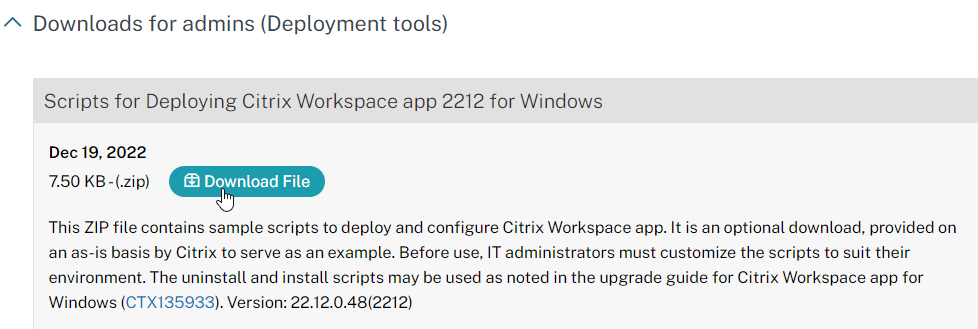
Also see CTA Dennis Span Citrix Receiver unattended installation with PowerShell.
Change Workspace App’s Store Configuration, including Reset Citrix Workspace
You can change Workspace app’s configured Store/Account with a couple command lines:
"C:\Program Files (x86)\Citrix\ICA Client\SelfServicePlugin\SelfService.exe" -deleteproviderbyname Corporate "C:\Program Files (x86)\Citrix\ICA Client\SelfServicePlugin\SelfService.exe" -init -createprovider Corporate https://storefront.corp.com/Citrix/Store/discovery
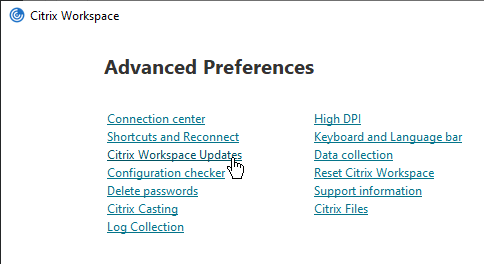
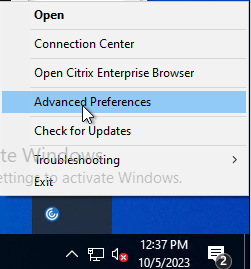
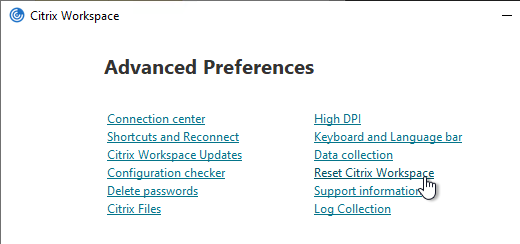
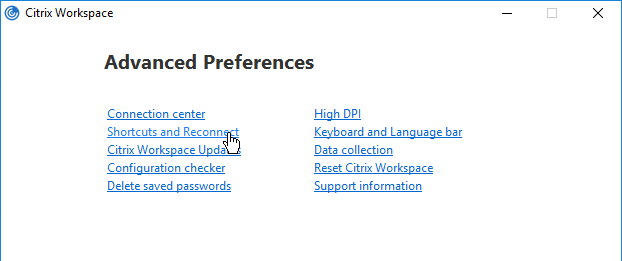
It is sometimes necessary to Reset Citrix Workspace by right-clicking the Workspace app systray icon, clicking Advanced Preferences, and clicking the Reset link. You can do this from the command line by running "C:\Program Files (x86)\Citrix\ICA Client\SelfServicePlugin\CleanUp.exe" -cleanUser -silent. See CTX140149 How to Reset Receiver Using the Command Line.
Workspace app Group Policy ADMX Template
Many of the Workspace app configuration settings must be configured in group policy. These Workspace app settings are only available after installing the GPO templates.
Alternatively, Citrix Cloud customers can use Global App Configuration Service to configure Workspace app. Today it’s a REST API, but Citrix has started adding a GUI at Workspace Configuration > App Configuration.
For GPO configuration:
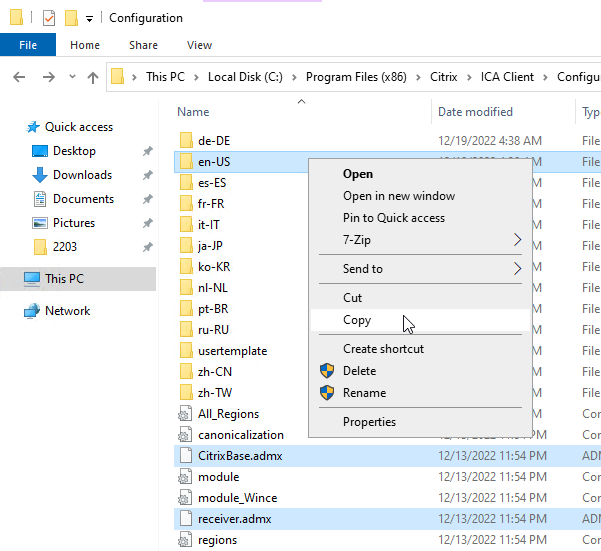
- From a machine that has Workspace app installed, find the .admx and .adml files in the C:\Program Files (x86)\Citrix\ICA Client\Configuration.
- Copy the CitrixBase.admx and receiver.admx files. Also copy the en-US folder. In Workspace app, the files are still named receiver.admx.
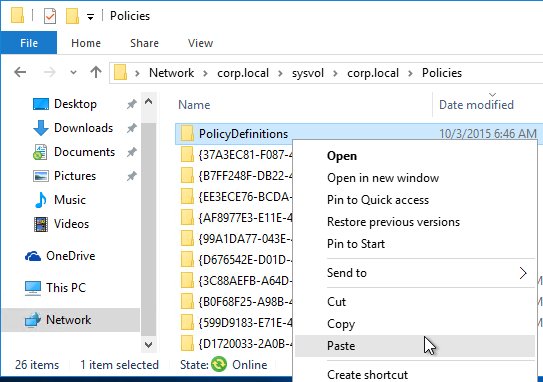
- Go to your domain’s SYSVOL share and in the Policies folder look for a PolicyDefinitions folder. If one exists, paste the .admx file directly into the PolicyDefinitions folder. If this folder doesn’t exist in SYSVOL, instead copy the .admx file to C:\Windows\PolicyDefinitions. Overwrite any existing Receiver ADMX files.
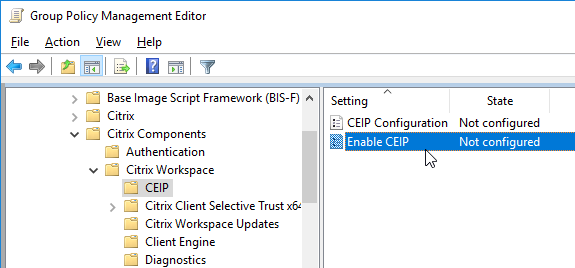
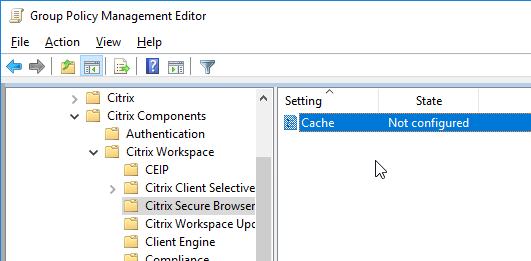
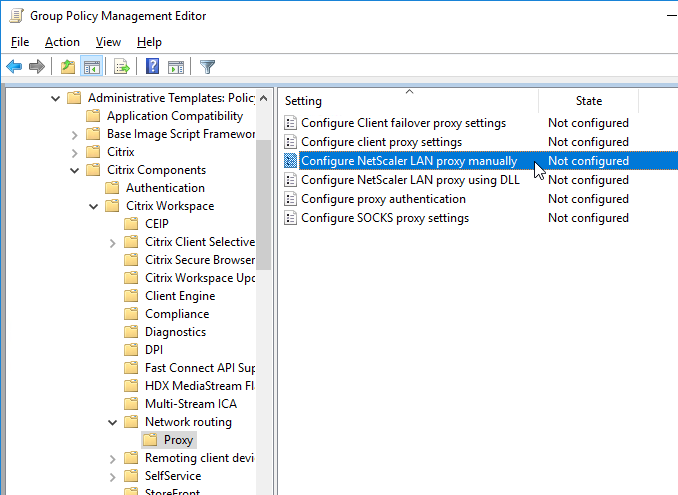
- The GPO settings can then be found at one of the following:
- Computer Configuration > Policies > Administrative Templates > Citrix Components > Citrix Workspace
- Computer Configuration > Policies > Administrative Templates > Citrix Components > Citrix Receiver
- For example, you can disable Customer Experience Improvement Program (CEIP) from here.
- See https://www.carlstalhood.com/delivery-controller-cr-and-licensing/#ceip for additional places where CEIP is enabled.
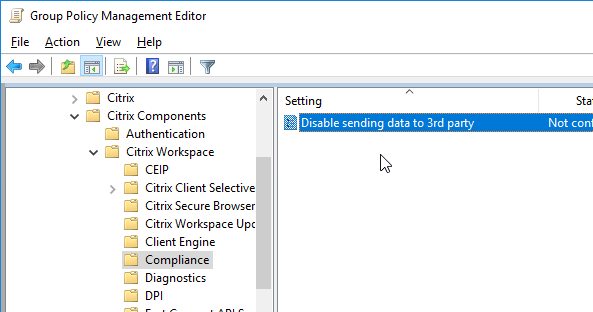
- Workspace app 1905 and newer has a setting to Disable sending data to 3rd party (e.g., Google Analytics).
- Workspace app 1905 and newer let you disable embedded browser caching.
- Workspace app 1905 and newer have NetScaler LAN Proxy under Network routing > Proxy.
- Workspace app 1808 and newer have User authentication | Single Sign-on for NetScaler Gateway.
- Citrix Workspace Updates, (aka AutoUpdate) can be configured using group policy. See Configuring Citrix Workspace Updates at Citrix Docs.
- Workspace app 1912 and newer can be configured to require in-memory ICA files only. The setting called Secure ICA file session launch is under the Client Engine node. See Citrix Docs for details on in-memory ICA files instead of writing ICA files to disk.
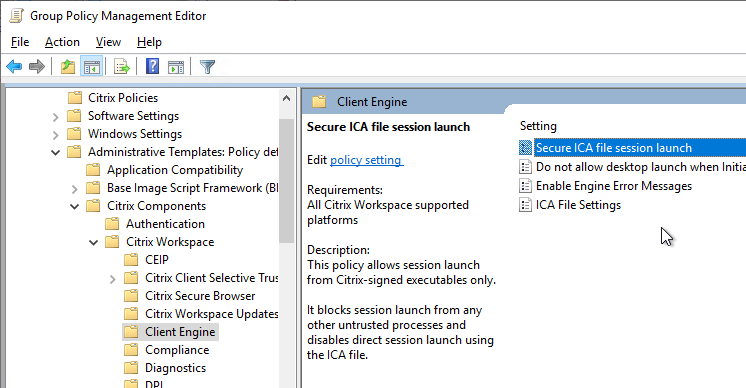
- The DPI node has a setting called High DPI that lets you disable DPI matching, which is enabled by default in Workspace App 2206 and newer.
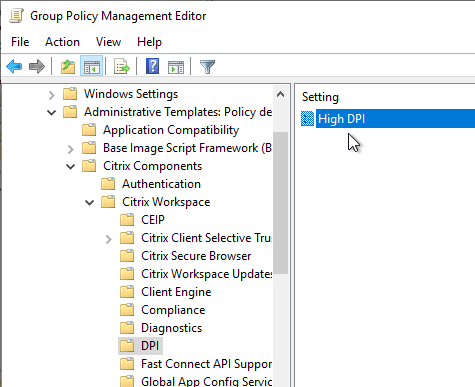
- Workspace app 2210 and newer let you use the GUI to re-enable High DPI.
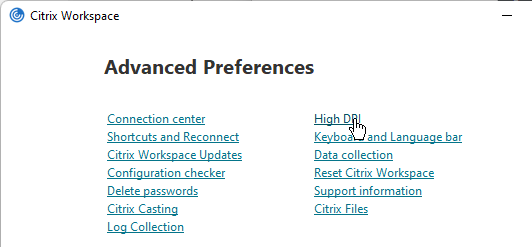
- Native resolution means DPI matching, whereas Yes means force high DPI.
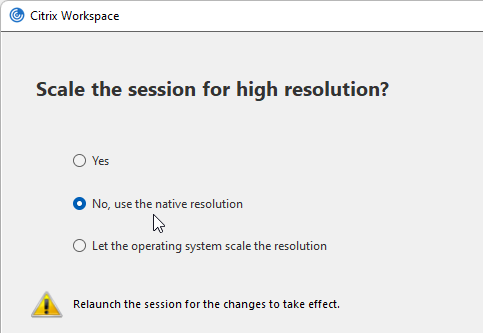
- Workspace app 2210 and newer let you use the GUI to re-enable High DPI.
- Workspace app has settings to hide Advanced Preferences, enable/disable showing the DPI option, and enable/disable H265.
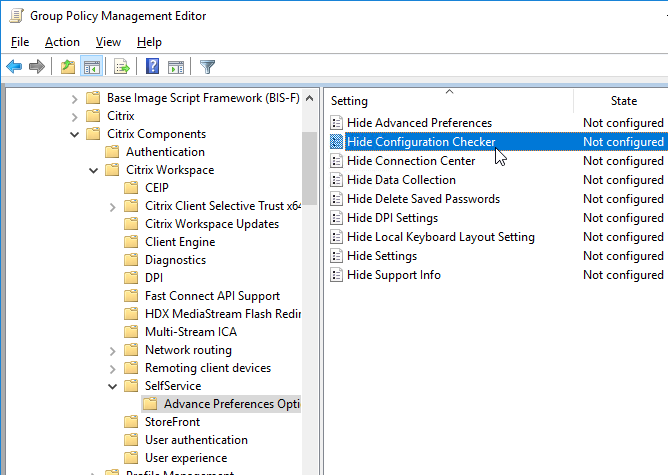
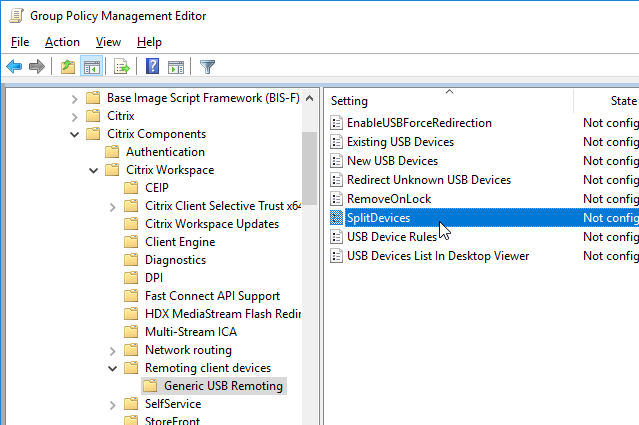
- Workspace app 4.8 and newer have SplitDevices GPO setting under Citrix Workspace | Remoting client devices | Generic USB Remoting. See Configuring composite USB device redirection at Citrix Docs.
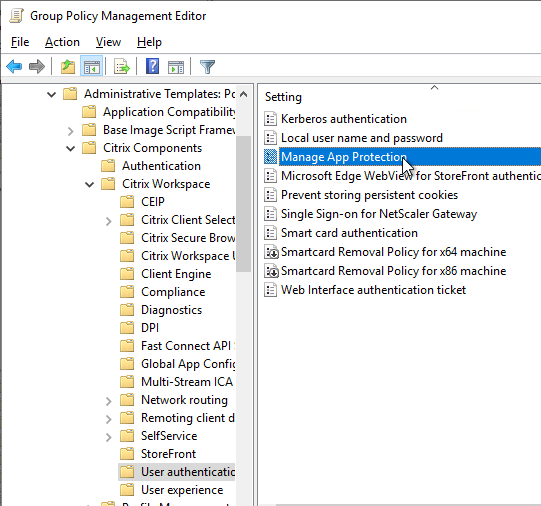
- Workspace app 2212 and newer by default disable App Protection for the authentication screen and icons list. To enable them, configure User authentication | Manage App Protection and SelfService | Manage App Protection.
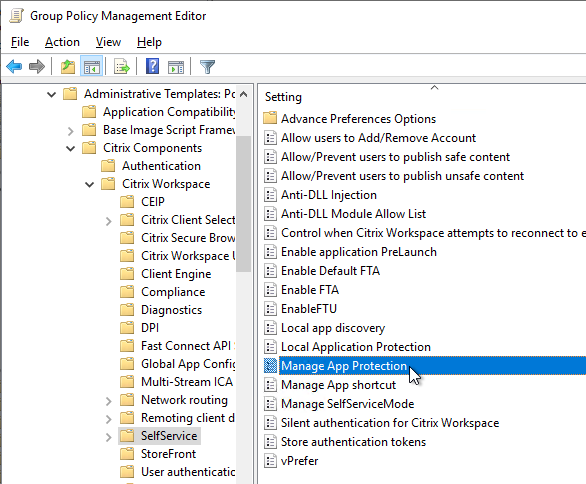
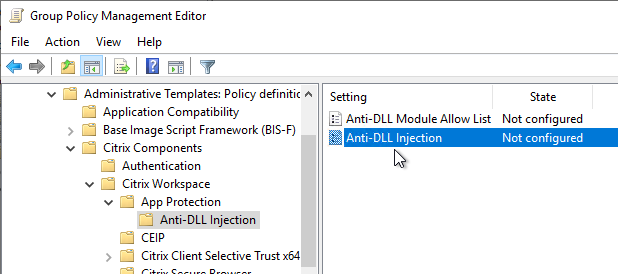
- Workspace app 2303 and newer have Anti-DLL Injection for App Protection. It is disabled by default. Enable it in a GPO at Citrix Components | Citrix Workspace | App Protection | Anti-DLL Injection. See Citrix Docs for details.

Pass-through Authentication
Citrix blog post – A Comprehensive Guide to Enabling Pass-Through Authentication with XenDesktop 7.5
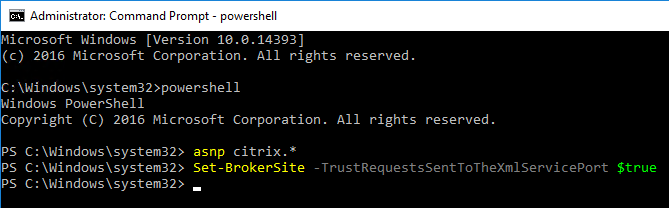
- Run the command
Set-BrokerSite -TrustRequestsSentToTheXmlServicePort $True from a Windows PowerShell command prompt on a Delivery Controller.
- In XenApp 6.5, this is a Citrix Policy > Computer > Trust XML Requests.
- Login to the PC as an administrator.
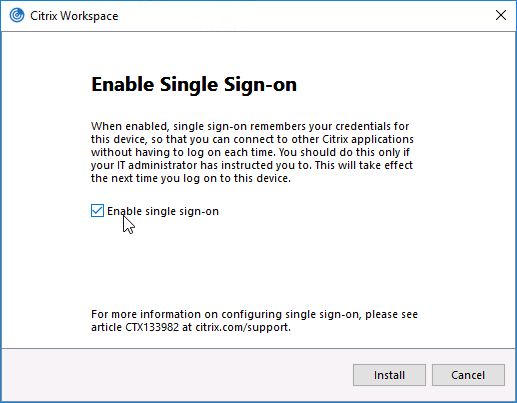
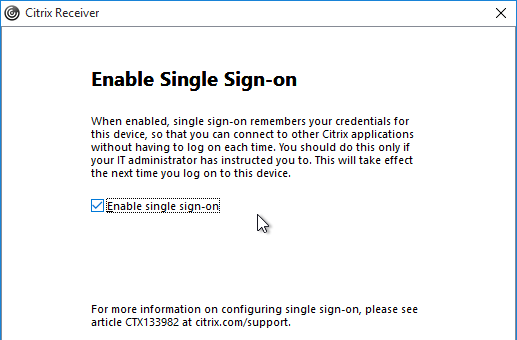
- If installing Workspace app, as an administrator, during installation, on the Enable Single Sign-on page, check the box next to Enable Single Sign-on. Then finish the installation.
- To verify that SSON is installed, go to C:\Program Files (x86)\Citrix\ICA Client and look for the file ssonsvr.exe.
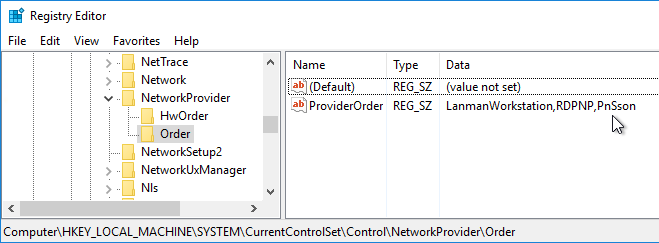
- And if you open regedit and go to HKLM\SYSTEM\CurrentControlSet\Control\NetworkProvider\Order, you should see PnSson in the ProviderOrder.
- Install the receiver.admx (and .adml) template into PolicyDefinitions if you haven’t already.
- Edit a GPO that is applied to the client PCs where the Workspace app is installed.
- Go to Computer Configuration > Policies > Administrative Templates > Citrix Components > Citrix Workspace.
- Expand Citrix Workspace and click User authentication.
- On the right, double-click Local user name and password.
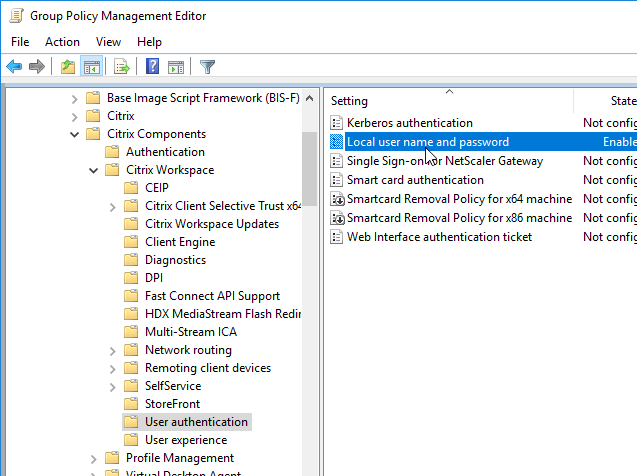
- Select Enabled and then check the box next to Allow pass-through authentication for all ICA connections. Click OK.
- In Workspace app 1808 and newer, you can enable Single Sign-on for NetScaler Gateway.
- Ensure that the internal StoreFront FQDN is in the Local Intranet zone in Internet Explorer. You can use a GPO to configure this on the client side.
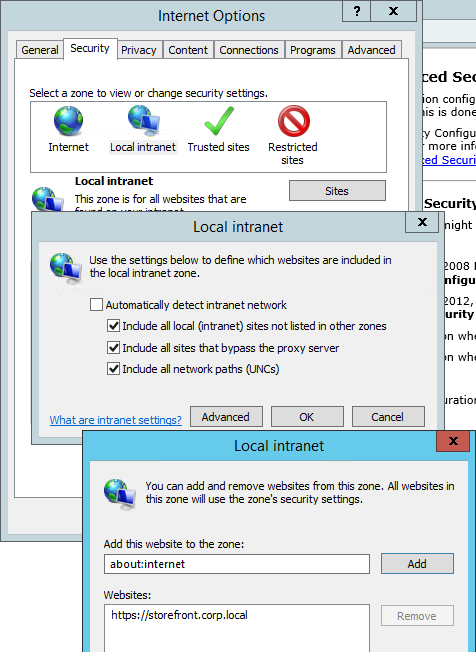
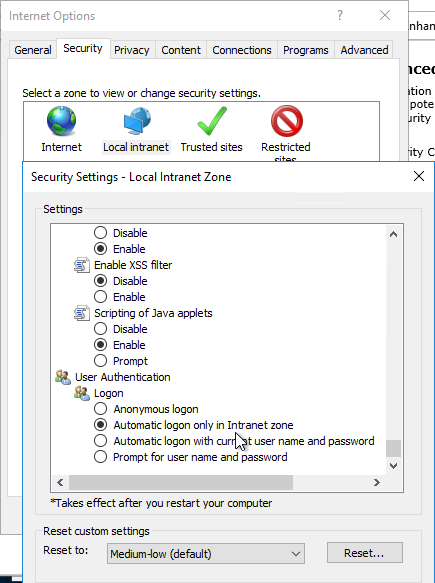
- Local Intranet zone should have Automatic logon only in Intranet zone enabled.
- For Windows 11 24H2 and newer, make sure the GPO setting Enable MPR notifications for the System is enabled at Computer Configuration | Policies | Administrative Templates | Windows Components | Windows Logon Options. Make sure HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\EnableMPRNotifications is set to 1 on the Workspace app machine.
- Logoff Windows and log back on. In Task Manager you should now see ssonsvr.exe. This won’t appear unless you logoff and log back on.
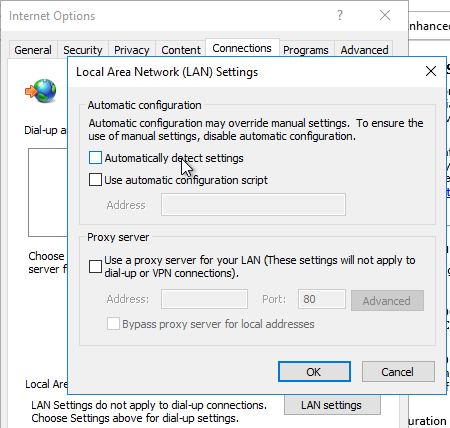
- If Workspace app won’t connect or is slow to enumerate icons, then you might have to disable Automatically detect settings in IE.
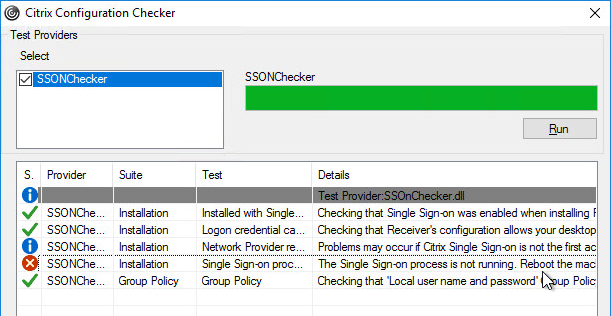
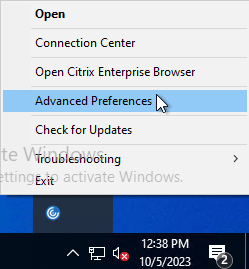
- Right-click the Workspace app icon and click Advanced Preferences.
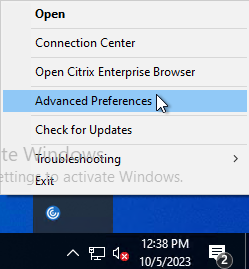
- Click Configuration Checker.
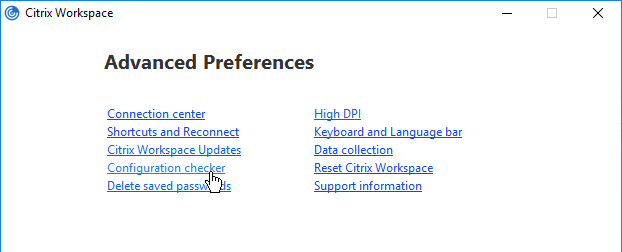
- Check the box next to SSONChecker and click Run.
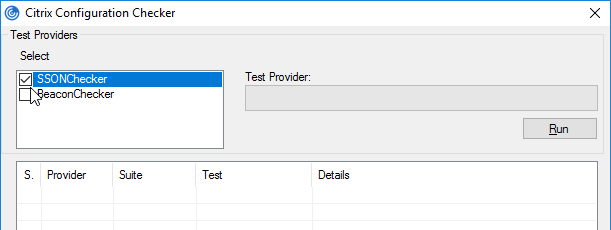
- The lines with red x will indicate the issue and corrective action.
StoreFront Accounts
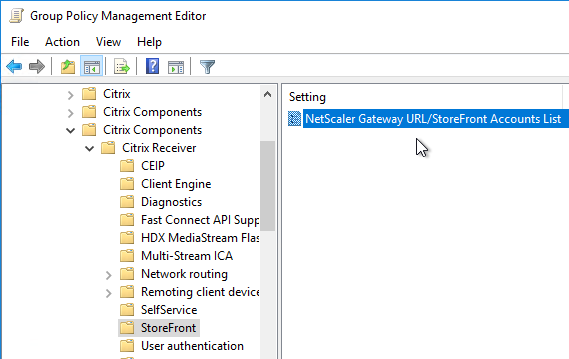
You can use a client-side GPO to add a store (Account) to Workspace app Self-Service.
- Install the receiver.admx (and .adml) template into PolicyDefinitions if you haven’t already.
- Edit a GPO that applies to endpoint devices that have Citrix Workspace app installed.
- Go to Computer Configuration > Administrative Templates > Policies > Citrix Components > Citrix Workspace > StoreFront.
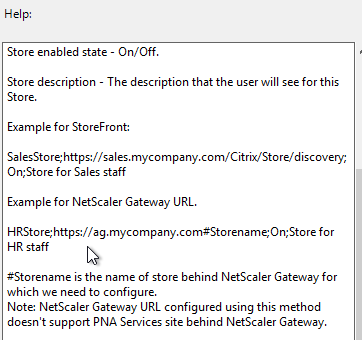
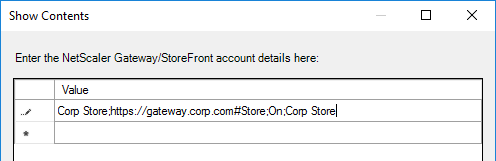
- On the right, double-click NetScaler Gateway URL/StoreFront Accounts List.
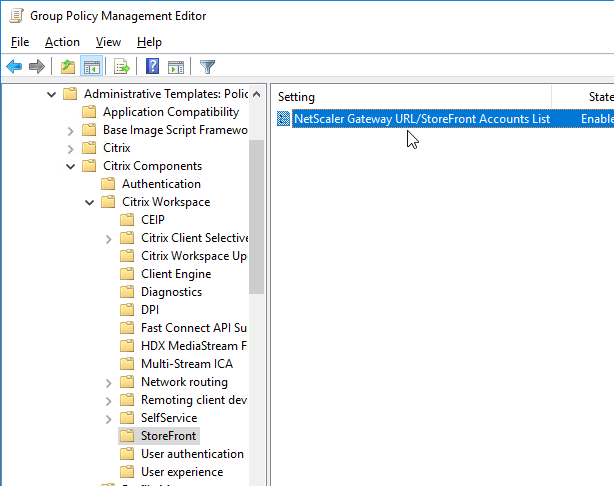
- Select Enabled, and then click Show.
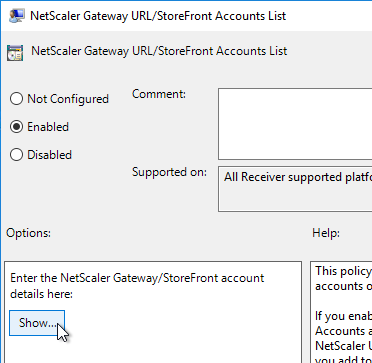
- Enter a store path based on the example shown in the Help box. Workspace app lets you enter a Gateway path. Then click OK.
- Note: Gateway paths work in GPO, but might not work when specified in the CitrixWorkspaceApp.exe installation command line.
Published Shortcuts and Reconnect
Citrix CTX200924 How to Customize App Shortcuts with Receiver for Windows
Workspace app has a user interface for setting Shortcut Paths. Right-click the Workspace app systray icon, click Advanced Preferences, and then click Shortcuts and Reconnect, or Settings Option.
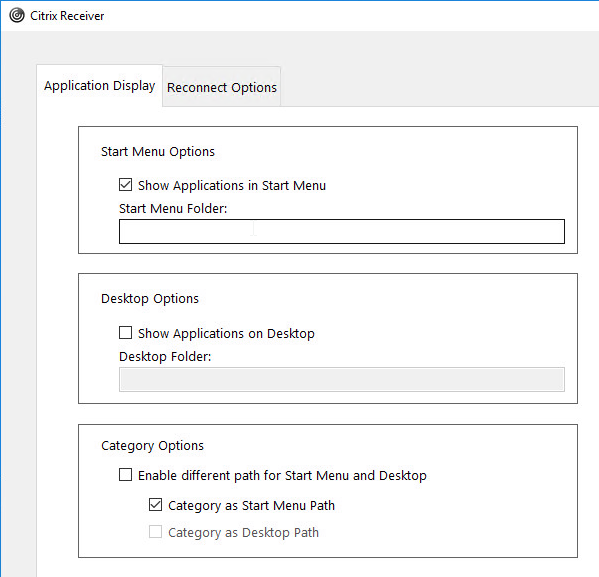
From Citrix Docs Configuring application delivery: There are several methods of controlling how Workspace app displays shortcuts on the Start Menu and Desktop as detailed below:
- Workspace app Registry values
- receiver.admx GPO Template
- From StoreFront in C:\inetpub\wwwroot\Citrix\Roaming\web.config
- Published App Keywords (e.g. prefer).
- Workspace app and Receiver 4.2.100 and newer supports published app Delivery configuration for adding the shortcut to the desktop. This only works if the app is a Favorite, or if Favorites are disabled, or Mandatory Store.
Under HKLM\Software\Wow6432Node\Citrix\Dazzle (or HKCU\Software\Wow6432Node\Citrix\Dazzle) are several registry values related to shortcuts. Some of the settings only apply if SelfServiceMode is set to False. Here are some common options:
- SelfServiceMode – set to False so Receiver disables the Self-Service interface and automatically places all published shortcuts on the Start Menu and/or Desktop. More details in Configuring application delivery at Citrix Docs.
- PutShortcutsOnDesktop – set to True to place every app on the desktop
- DesktopDir – Workspace app places every shortcut on the desktop so it’s probably best to place them in a folder.
- StartMenuDir – If there is potentially a conflict between local apps and remote apps, then you should place the Start Menu shortcuts in a folder.
- PreferTemplateDirectory (with KEYWORDS:prefer=shortcutname) – copies the shortcutname from the template directory to the Start Menu and/or Desktop.
If you import the receiver.admx (and .adml) into the PolicyDefinitions folder, under Computer Configuration > Administrative Templates > Citrix Components > Citrix Workspace (or Receiver) is a node called SelfService.
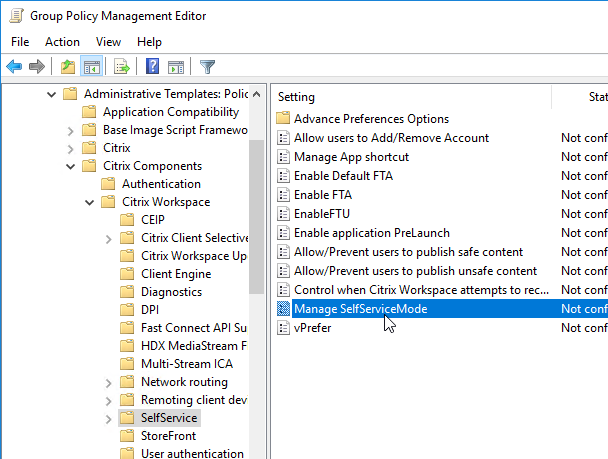
Disable the Manage SelfServiceMode setting to hide the Workspace app Window.
Enable the Manage App shortcut setting to control placement of shortcuts.
Workspace app and Receiver 4.2.100 and newer have the ability to configure (or disable) Workspace Control using group policy. Enable the setting Control when Citrix Workspace attempts to reconnect to existing sessions and configure it as desired.
Prelaunch
Staring with Receiver 4.2, prelaunch is automatically enabled if Workspace app is installed with SSON enabled. Otherwise, set registry values to enable prelaunch. Receiver 4.2.100 prevents the prelaunch icon from appearing on the Start Menu.
- HKLM\Software\[Wow6432Node\]Citrix\Dazzle
- EnablePreLaunch (REG_SZ) = true or false
Additional customizations can be configured at:
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\ICA Client\Prelaunch
- Name: State
- REG_SZ: 0 = disable, 1 = just-in-time pre-launch, 2 = scheduled pre-launch
- Name: Schedule
- REG_SZ: HH:MM|M:T:W:TH:F:S:SU where HH and MM are hours and minutes. M:T:W:TH:F:S:SU are the days of the week. For example, to enable scheduled pre-launch on Monday, Wednesday, and Friday at 1:45 p.m., set Schedule as Schedule=13:45|1:0:1:0:1:0:0 . The session actually launches between 1:15 p.m. and 1:45 p.m.
- Name: UserOverride
- REG_SZ: 0 = HKLM overrides HKCU, 1 = HKCU overrides HKLM
Device Access Behavior (Client Selective Trust)
When connecting to a XenApp/XenDesktop session, you might see the following:
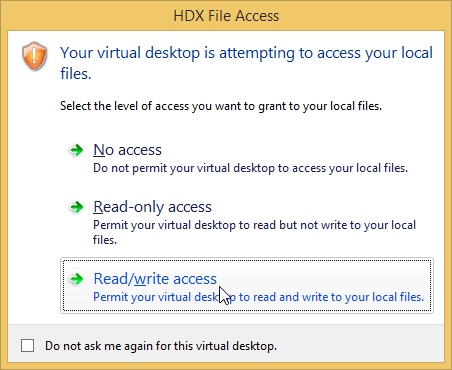
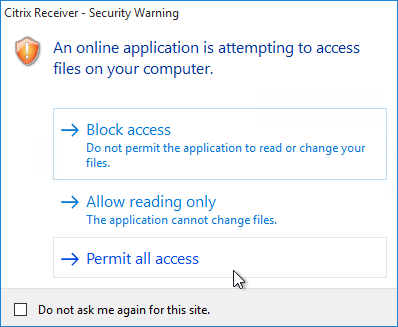
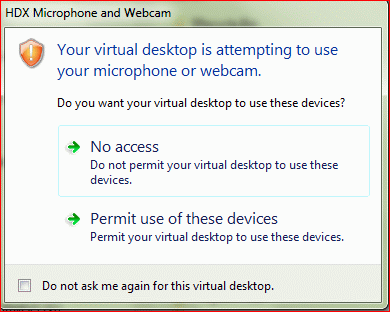
To configure the default behavior, see the Citrix Knowledgebase article How to Configure Default Device Access Behavior of Receiver, XenDesktop and XenApp. Note: there is a bug fixed in Receiver 4.2.100 and newer.
- Download the ADMX file from http://support.citrix.com/article/CTX133565.
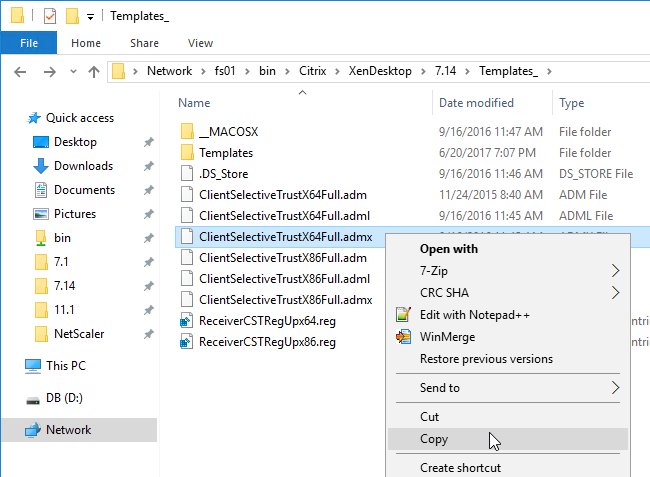
- Copy the .admx and .adml files to PolicyDefinitions (Sysvol, or C:\Windows).
- The .adml file goes in the en-US folder.
- Edit a GPO that applies to the endpoint devices that are running Receiver.
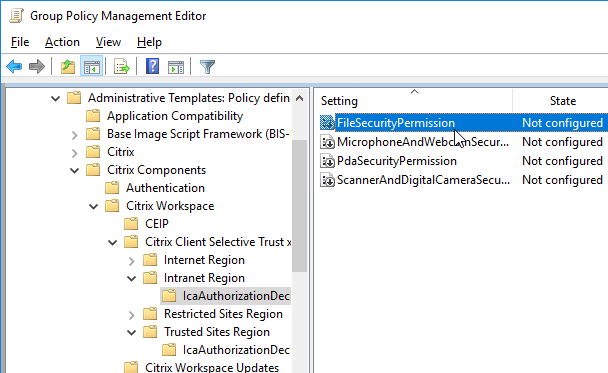
- Go to Computer Configuration | Policies | Administrative Templates | Citrix Components | Citrix Workspace (or Receiver) | Citrix Client Selective Trust (x64).
- Enable the setting Create Client Selective Trust Keys.
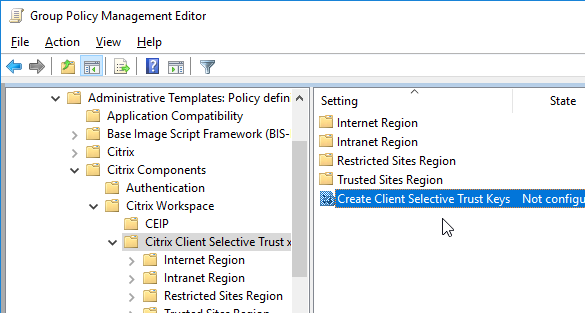
- Then expand the regions, and configure the permission settings as desired.
Desktop Lock
As an alternative to Workspace app Desktop Lock, see Transformer in Citrix Workspace Environment Manager.

External links:
- Dale Scriven YouTube video – Citrix Desktop Lock installation and configuration
- Jarian Gibson and Andrew Morgan – Citrix Receiver Desktop Lock
- An alternative to Desktop Lock – ThinKiosk
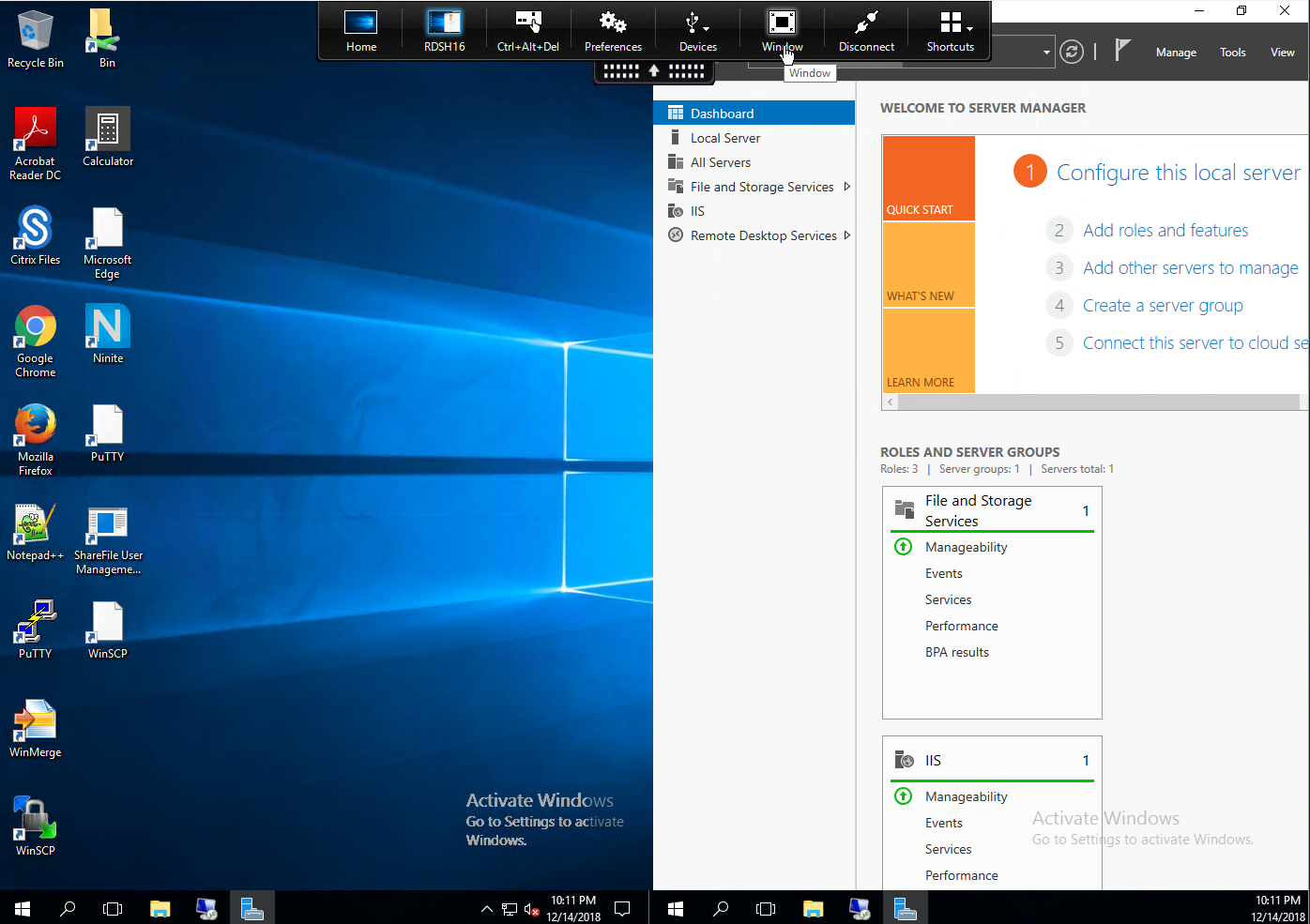
Use Studio to configure Workspace app Accounts in Published Desktop
In published desktops, Workspace app can be used for placement of shortcuts on the user’s Start Menu and Desktop. Use group policy to hide the common program groups and then use Workspace app to place published applications back on the Start Menu and Desktop based on user’s group membership and subscription preference.
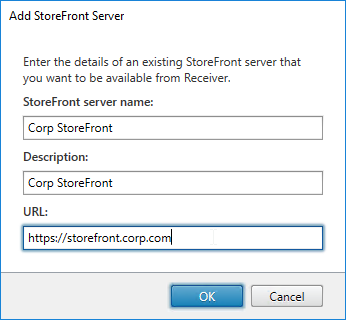
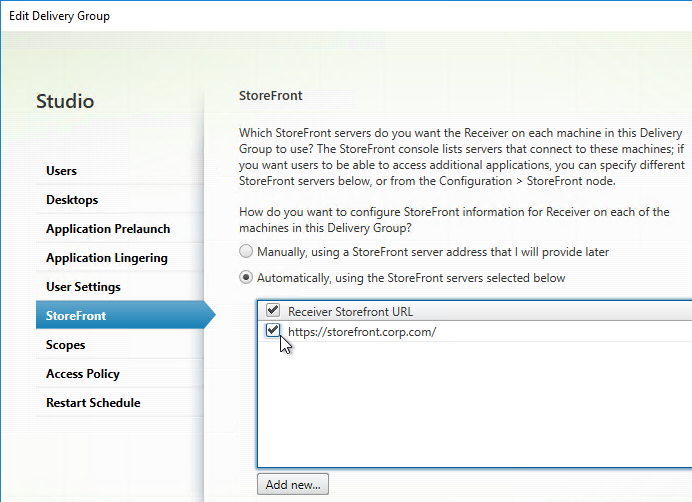
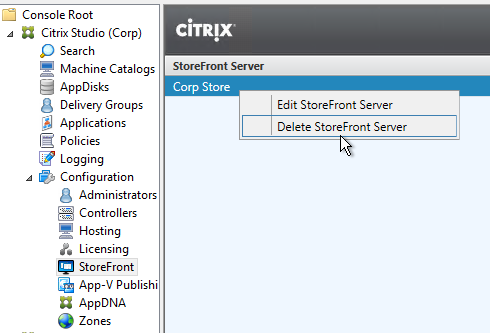
- In Citrix Studio, on the left, expand the Configuration node, right-click StoreFront and click Add StoreFront.
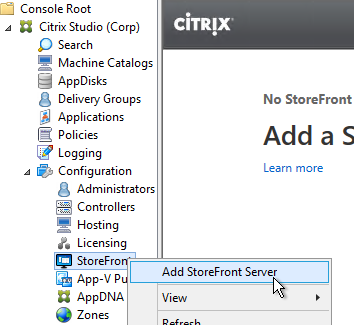
- Enter a descriptive name for the StoreFront server.
- Enter the internal https URL of the load balanced StoreFront servers. Add the path to your store (e.g. /Citrix/Store) and then /discovery on the end of the URL. The full URL would be similar to https://citrix.corp.com/Citrix/Store/discovery. Click OK.
- Edit a Delivery Group that has a published desktop and Citrix Workspace app installed.
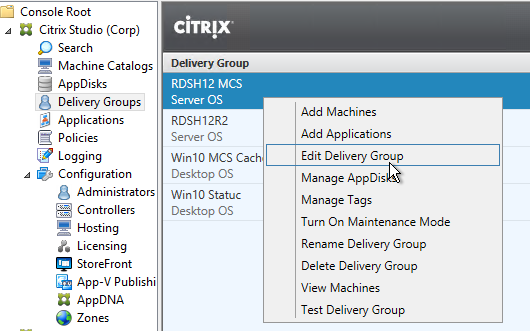
- On the StoreFront page, change the selection to Automatically, using the StoreFront servers selected below, and then check the box next to the StoreFront URL. Click OK. Now when users launch the published desktop, Workspace app will be automatically configured with this URL.
Published Desktop – use Workspace app to control Shortcuts
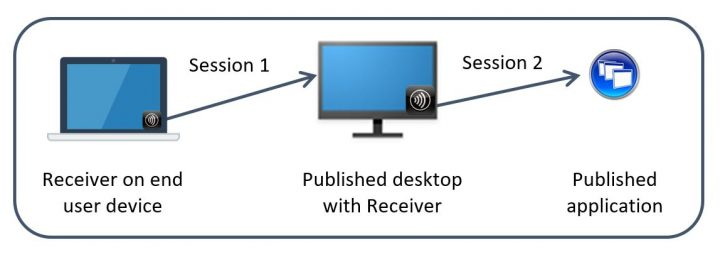
If you install Workspace app inside a published desktop (Workspace app on a VDA), then Workspace app can get icons from StoreFront and put those icons on the user’s published desktop Start Menu and Desktop. This is an alternative to using a User Experience Management product to control shortcut placement.
Note: Workspace app tends to be slow to create Start Menu shortcuts, so make sure you perform a Proof of Concept to determine how this functionality impacts logon times.
Configuration of Workspace app inside a published desktop is simplified if you have the following minimum versions:
- Workspace app installed inside the VDA
- VDA 7.17 or newer
- StoreFront 3.14 or newer
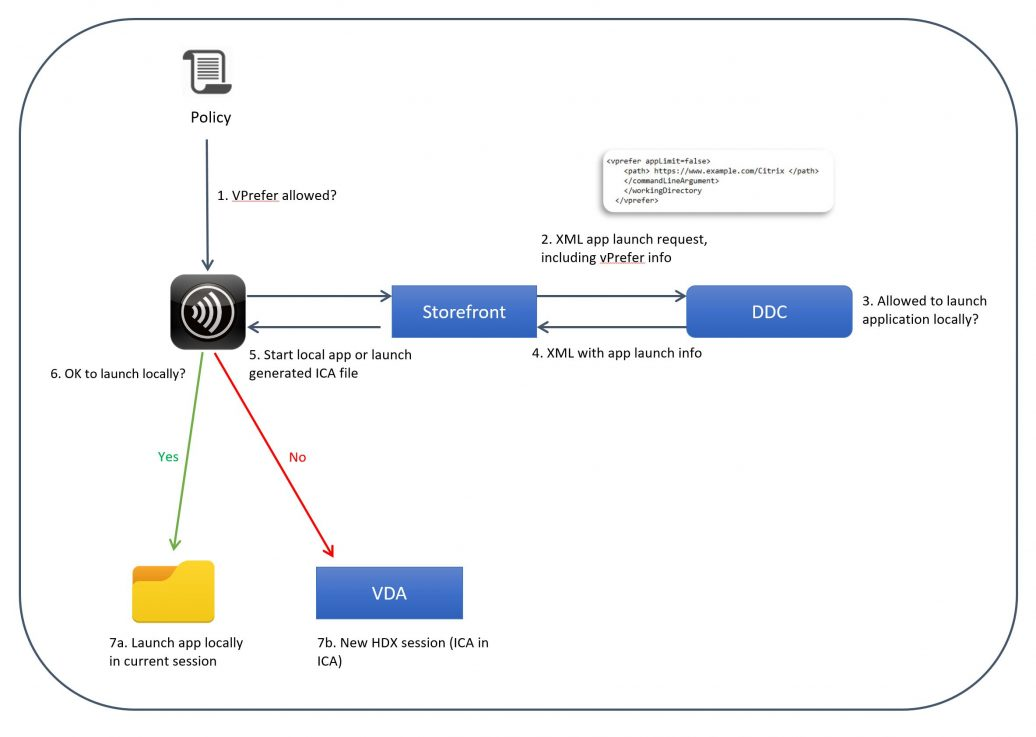
If you meet these minimum version requirements, then Workspace app installed in the VDA automatically tries to launch published applications on the same local VDA rather than trying to launch them from a different VDA (aka double-hop). This feature is called vPrefer.
- If you don’t meet these minimum version requirements, then you’ll need to use the older Prefer Keyword method of handling Workspace app shortcuts as detailed later.
- For a detailed explanation of vPrefer, see Citrix Blog Post VPrefer: Session Sharing Between a Published Desktop and a Published Application Made Easy
Do the following for all versions of Workspace app, VDA, and StoreFront, whether using the Prefer keyword or not:
- Make sure Workspace app or Receiver version 4.11 or newer is installed on the VDA.
- Install the Workspace app ADMX files if you haven’t already. For vPrefer, make sure they are the ADMX files from Workspace app.
- Enable the Group Policy setting Remove common program groups from Start Menu and apply it to non-administrators.
- This removes all Public (aka All Users) Start Menu shortcuts. Workspace app will re-add the shortcuts based on user group membership.
- On the VDA, configure the following Workspace app Registry keys (or corresponding settings in the receiver.admx GPO template):
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\WSCReconnectMode=”0″ so Workspace app doesn’t try to reconnect to the published desktop you’re already running.
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\SelfServiceMode to False. This turns off the Workspace app Self-Service GUI and acts like all icons are subscribed. Otherwise, only subscribed (favorited) icons would be placed on the Start Menu and Desktop.
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\UseCategoryAsStartMenuPath = True. This creates a Start Menu folder based on the published app’s configured Category.
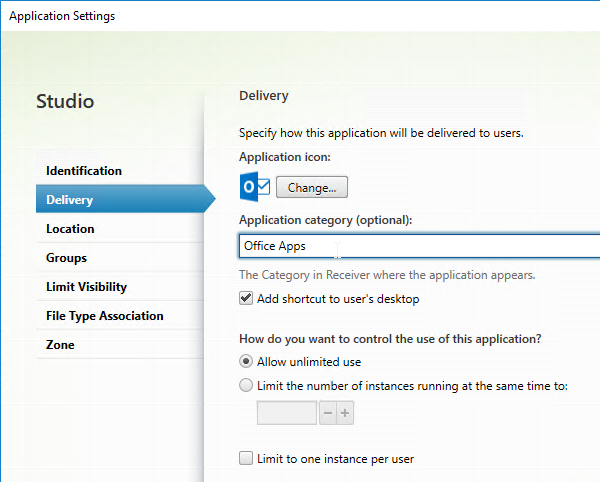
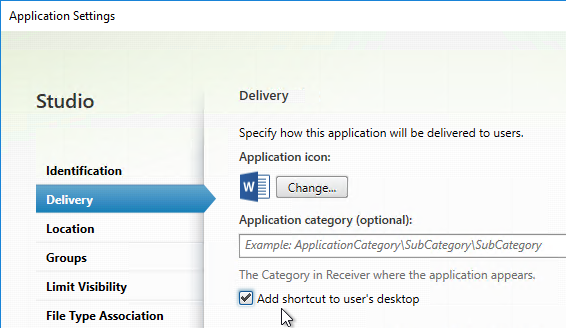
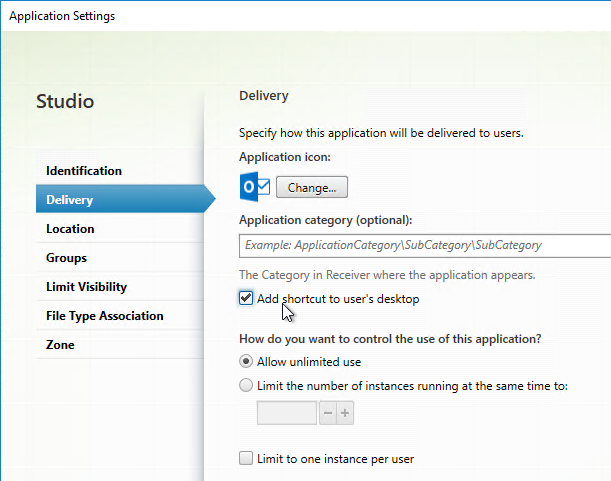
- Configure each desired published app to Add shortcut to user’s desktop.
- Or, configure HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\PutShortcutsOnDesktop = True to place all icons on the desktop.
- To control icon placement, configure the following registry values:
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\StartMenuDir to place published applications in a sub-folder. Note: Windows Server 2012 and Windows 10 and newer only supports a single level of Start Menu folders, so setting this effectively turns off published app categories.
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\DesktopDir to place published applications in a sub-folder on the desktop.
- Pass-through authentication:
- In a GPO that applies to the VDA, import the receiver.admx file, and set Local user name and password to Enabled. Check the box next to Allow pass-through authentication for all ICA connections.
- If you’re using Gateway internally, and if Workspace app 1808 or newer, then also enable Single Sign-on for NetScaler Gateway.
- In a user-level GPO that applies to the VDA, add the StoreFront FQDN to the Local Intranet zone. Make sure it is not in the Trusted Sites zone, or enable Automatic logon with current user name and password for the Trusted Sites zone.
- Make sure ssonsvr.exe is running after you login to the VDA. If not, troubleshoot it.
- When configuring Citrix Profile Management, make sure !ctx_startmenu! is not excluded from roaming.
- In Citrix Studio, configure a Delivery Group with delivery type = Desktop and Applications. Assign users to the delivery group, and the individual published applications (if visibility is limited).
- In Citrix Studio, edit each published application, and on the Delivery tab, specify a category. This will become the Start Menu folder name.
- If Workspace app Self Service Mode (GUI) is enabled, in Studio, edit each application, and add KEYWORDS:Auto and/or KEYWORDS:Mandatory to the published application description. This forces the applications to be subscribed/favorited. Only subscribed (or Favorite) apps are displayed in the Start Menu and Desktop. Unless you disable Workspace app’s SelfService interface as described earlier.
- Another option is to go to the StoreFront Console, click Stores on the left, and on the right, click Configure Store Settings, and click Disable User Subscriptions. This causes all apps to appear on the Start Menu and/or Desktop depending on Workspace app configuration.
- Create a group policy that applies to VDAs, and configure the group policy to define the Store URL for Workspace app similar to https://citrix.corp.com/Citrix/Store/discovery. Replace the FQDN with your load balanced StoreFront FQDN. Also replace the path to the store with your store path. Make sure there is /discovery on the end. By default, Workspace app and Receiver only support https.
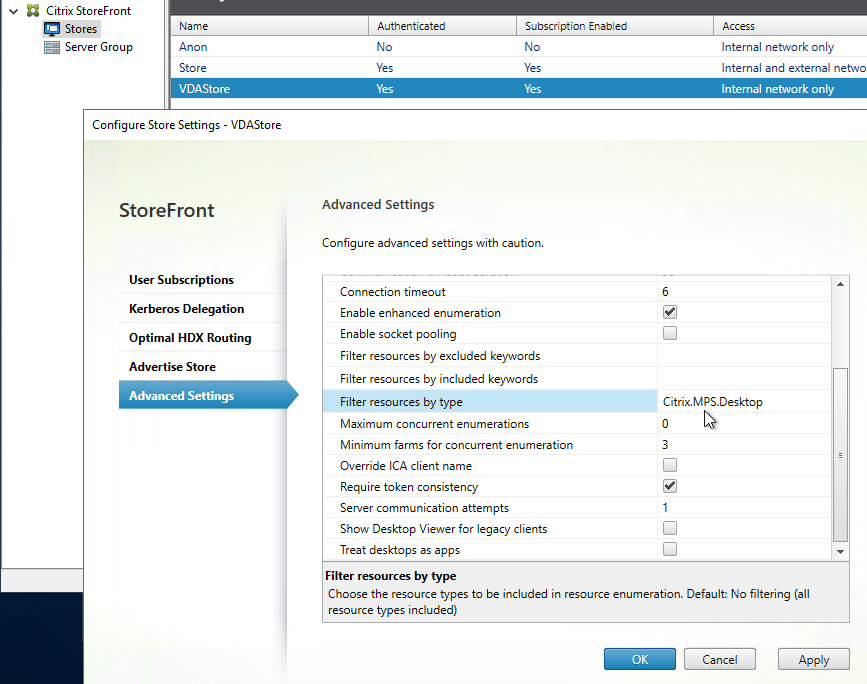
- Your StoreFront store probably delivers both application and desktop icons. If you want to filter out the desktop icons, then create a new StoreFront store, and configure the Workspace app on the VDA to connect to the new Store.
- In StoreFront Console, click the store for VDAs, and click Configure Store Settings. On the Advanced Settings page, in the Filter resources by type row, choose Citrix.MPS.Desktop.
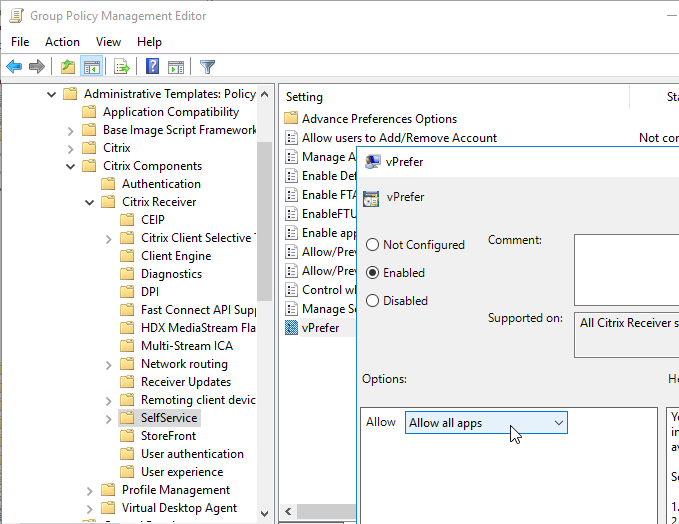
- For vPrefer in Workspace app, VDA 7.17 (or newer), and StoreFront 3.14 (or newer), edit a GPO that applies to the VDAs.
- Go to Computer Configuration | Policies | Administrative Templates | Citrix Components | Citrix Workspace (or Receiver) | SelfService.
- Edit the setting vPrefer. This setting is only in Workspace app ADMX templates from Workspace app.
- Set it to Allow all apps. Source = 7.17 vPrefer – not working with 32Bit Apps at Citrix Discussions.
- On your Delivery Controller, in PowerShell, run set-brokersite -TrustRequestsSentToTheXmlServicePort $true
- This is required for Pass-through Authentication from Workspace app.
- Configure your client devices to connect to the published desktop.
- When users connect to the published desktop, Workspace app will auto-launch and hopefully auto-login.
- If Workspace app Self-Service Mode is disabled, all published applications should automatically appear in the Start Menu and Desktop.
- If Workspace app Self-Service Mode is enabled, then only applications with KEYWORDS:Auto and/or KEYWORDS:Mandatory in the published application description will be displayed. Users can open the systray icon to subscribe to more applications.
- Users can copy icons from the Start Menu to the desktop. Make sure the user Copies the icon and doesn’t Move it.
- Users can then launch applications directly from the Start Menu, from the Desktop, or from the Workspace app (if the Self-Service interface is enabled).
- If Workspace app 4.11 (or newer), VDA 7.17 (or newer), and StoreFront 3.14 (or newer), then vPrefer is enabled by default. When launching an app icon that came from Workspace app, Workspace app checks the local VDA machine to see if the application can be launched on the local VDA instead of by creating a new Citrix double-hop session.
- If the application is installed locally on the VDA then the local application shortcut should launch quickly. If the application is on a different delivery group then a second (double-hop) Citrix HDX/ICA connection will be established.
- If the user deletes Workspace app shortcuts from the Start Menu, you can get them back by going to the systray icon and refreshing the applications. Or sometimes you have to reset Workspace app.
If you are running components older than Receiver 4.11, VDA 7.17, and StoreFront 3.14, then you’ll need to configure the prefer keyword to get Receiver delivered icons to launch on the local VDA instead of in a new double-hop Citrix connection.
- Enable the Group Policy setting Remove common program groups from Start Menu and apply it to non-administrators.
- For applications that are installed on the same VDA that is publishing the desktop, configure Group Policy Preferences to recreate the application shortcuts based on Active Directory group membership. Applications on other delivery groups are handled by Receiver.
- Or use the prefer keyword to copy shortcuts from the PreferTemplateDirectory.
- On the VDA, configure the following Receiver Registry keys (or corresponding settings in the receiver.admx GPO template):
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Dazzle\PreferTemplateDirectory = a UNC path or local path containing shortcuts to be copied by the prefer keyword. This can point to C:\ProgramData\Microsoft\Windows\Start Menu.
- In Citrix Studio, configure a Delivery Group with delivery type = Desktop and Applications. Assign users to the Delivery Group and the applications (if visibility is limited).
- In Studio, edit each application and change KEYWORDS:Prefer to KEYWORDS:prefer. Notice the lower case p. It doesn’t work with uppercase P.
- With the prefer keyword, if you publish an application that is also created using Group Policy Preferences, the Group Policy Preferences icon will take precedence. This is good. Otherwise the Receiver published application icon would result in a new Citrix double-hop session.
- See Ralph Jansen Citrix Receiver 4.1 Prefer keyword examples
- If using the prefer keyword with the PreferTemplateDirectory, enter it as KEYWORDS:prefer=shortcutname where shortcutname is the name of the shortcut that is copied from the Template directory.
- In Studio, edit each application and change KEYWORDS:Prefer to KEYWORDS:prefer. Notice the lower case p. It doesn’t work with uppercase P.
- Configure your client devices to connect to the published desktop.
- When users connect to the published desktop, Group Policy Preferences will create shortcuts to local applications.
- Receiver will auto-launch and hopefully auto-login.
- If Receiver Self-Service Mode is disabled, all published applications should automatically appear in the Start Menu and Desktop.
- If Receiver Self-Service Mode is enabled then only applications with KEYWORDS:Auto and/or KEYWORDS:Mandatory in the published application description will be displayed. Users can open the systray icon to subscribe to more applications.
- For published applications with KEYWORDS:prefer=shortcutname, Receiver should copy icons from the template directory to the Start Menu and/or Desktop. See below for considerations.
- Users can copy icons from the Start Menu to the desktop. Make sure the user Copies the icon and doesn’t Move it.
- Users can then launch applications directly from the Start Menu, from the Desktop, or from the Receiver (if Self-Service interface is enabled).
- If a local shortcut (e.g. Group Policy Preferences shortcut, or copied from template directory) matches a published application with KEYWORDS:prefer then the local shortcut will override the published application icon.
- If the application is installed locally on the VDA then the local application shortcut should launch quickly. If the application is on a different delivery group then a second (double-hop) Citrix HDX/ICA connection will be established.
- If the user deletes Receiver shortcuts from the Start Menu, you can get them back by going to the systray icon and refreshing the applications. Or sometimes you have to reset Receiver.
Notes regarding Prefer Template Directory
- Prefer Template Directory can point to C:\ProgramData\Microsoft\Windows\Start Menu, which is the All Users Start Menu.
- The shortcuts copied from the Prefer Template Directory are renamed to match the published app name.
- For prefer local apps, any command line parameters specified in the published app are ignored. If you need these command line parameters, add them to the shortcut in the Prefer Template Directory.
- If you have multiple published apps pointing to the same prefer local shortcut, then only one copy will be made, and it will have the name of only one of the published apps. To workaround this, in the Prefer Template Directory, create separate shortcuts for each published app, and adjust the published app prefer keyword accordingly.
- Jan Hendrik Meier Automatic Shortcut generation for local installed applications in a Citrix XenDesktop / XenApp 7.x environment has a script that can create shortcuts based on the published apps with prefer keyword. These shortcuts can then be copied to your Prefer Template Directory.
How to Script/Automate Workspace app and Receiver Self-Service
From Citrix Knowledgebase article Driving the Citrix Receiver Self-Service Plug-in Programmatically: by default, Workspace app Self-Service (SSP) activities are driven by user interaction. However, SSP exposes sufficient information for its activities to be scripted.
When SSP builds a shortcut, it builds it to a small stub application in a file %appdata%\Citrix\SelfService\app-name-with-spaces-removed.exe for each resource. These files allow SSP to create a fake ‘install’ record for Add/Remove Software. Running these .exe files causes the application to launch. Note: Workspace app and Receiver 4.3.100 and newer don’t create stubs by default. To enable, set HKLM\Software\Wow6432Node\Citrix\Dazzle\AlwaysUseStubs (REG_SZ) = true.
If you want to drive SSP directly for launch instead of through an .exe stub, look at the keys under HKCU\Software\Microsoft\Windows\CurrentVersion\Uninstall. There will be keys in there named farm-name@@server-farm-name.app-friendly-name. In these keys you’ll find a LaunchString value that shows the relevant parameters. These parameters are user-independent and can therefore be cloned from a reference user to a general case. You can copy and reuse these parameters without interpretation.
Running the command selfservice.exe –init –ipoll –exit starts SSP, performs a refresh (interactive poll) from the current provider, and forces a clean exit.
Additional command line parameters are detailed at Driving the Citrix Receiver Self-Service Plug-in Programmatically.
Citrix Workspace app come with a .dll file that implements the Citrix Common Connection Manager SDK. You can use the CCM SDK to do the following:
- Launch Sessions
- Disconnect Sessions
- Logoff Sessions
- Get Session Information
Citrix was kind enough to develop a PowerShell module that calls functions from the .dll. Get the CCMPowershellModule from Github. The PowerShell module contains functions like the following:
- CCMTerminateApplication
- CCMLaunchApplication
- CCMGetActiveSessionCount
- CCMDisconnectAllSessions
Launcher Scripts
Ryan C Butler Storefront ICA file creator at Github. See Create an ICA File from Storefront using PowerShell or JavaScript for more info.
Stan Czerno – Powershell Script to launch one or more Published Applications from Citrix Storefront 2.x through 3.11: the script launches a browser, connects to StoreFront (or NetScaler Gateway), logs in, and launches an icon. This is a very well-written script that uses a .dll file from Citrix Workspace app to display session information.
Citrix Solutions Lab StoreFront Launcher Script at Github. It attempts to closely resemble what an actual user would do by:
- Opening Internet Explorer.
- Navigating directly to the Receiver for Web site or NetScaler Gateway portal.
- Completing the fields.
- Logging in.
- Clicking on the resource.
- Logging off the StoreFront site.
David Ott StoreFront App/Desktop Launch Testing Script uses Internet Explorer to login to StoreFront and launch a resource. Sends email with the result. Uses wficalib.dll to get session information.
Microsoft Teams
Citrix and Microsoft jointly support the delivery of Microsoft Teams from Citrix Virtual Apps and Desktops using optimization for Microsoft Teams. The Teams optimization components are built into VDA and Workspace app. There is no need to install anything separately. The feature is based on Browser Content Redirection so don’t exclude that feature when installing the VDA.
Microsoft Teams optimization/offloading requires the following:
- Newest version of Microsoft Teams machine-wide installation (ALLUSER=1)
- Newest version of Citrix VDA
- Newest version of Citrix Workspace app.
Feature matrix and version support at Citrix Docs shows the required versions of Teams, Citrix VDA, and Citrix Workspace app for various Teams features.
See Citrix Docs Optimization for Microsoft Teams.
Troubleshooting – Citrix QuickLaunch
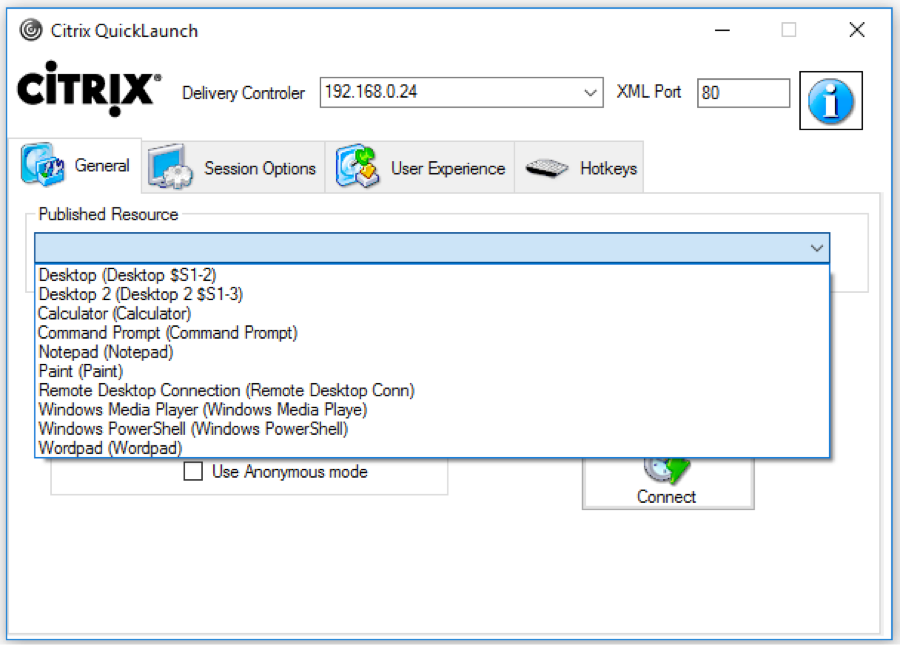
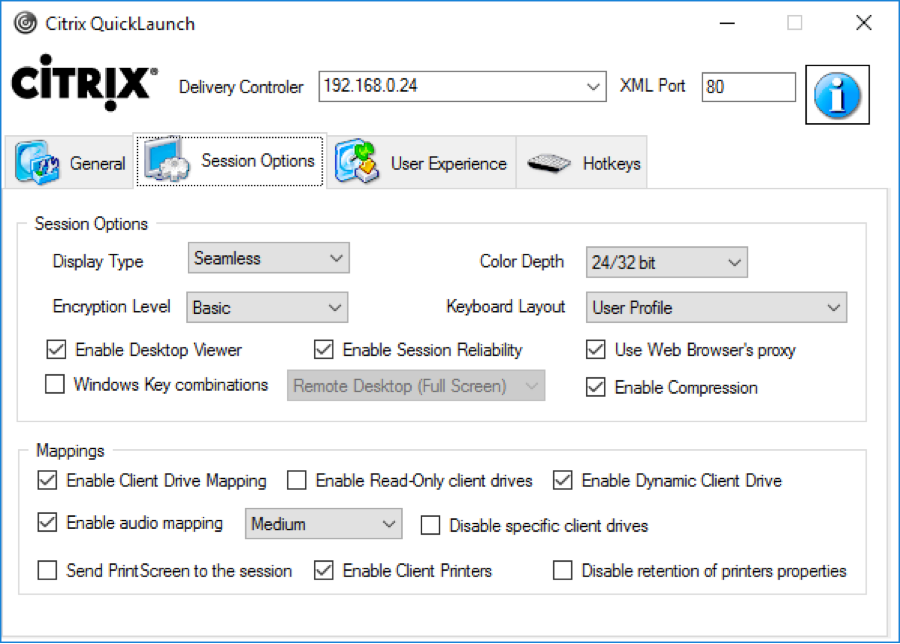
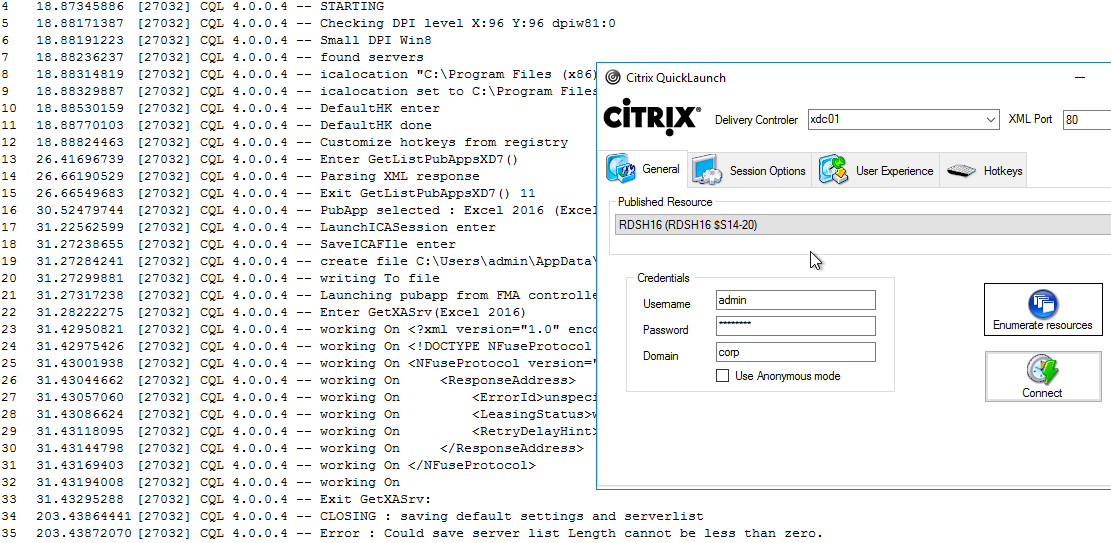
Citrix CTX219718 QuickLaunch Tool (Testing Application and Desktop Launch) lets you launch Citrix sessions directly from a Controller without needing StoreFront.
You enter a Controller address, credentials, and then it shows you the published resources. You can pick a resource, edit properties on the other tabs, and then Connect. This allows you to easily try different connection properties.
If you run into problems launching a session, use Sysinternals DebugView while running CQL in Debug mode (/debug switch).
Troubleshooting – Workspace app Logging
In Workspace app 2309 and newer, if you right-click the Workspace app icon in the system tray, there’s a Troubleshooting menu with a Collect Logs option.
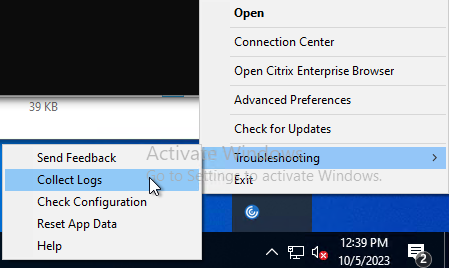
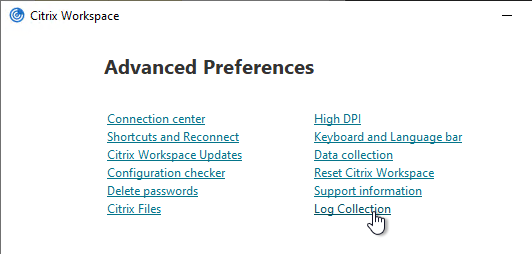
You can also access Log Collection from Advanced Preferences.
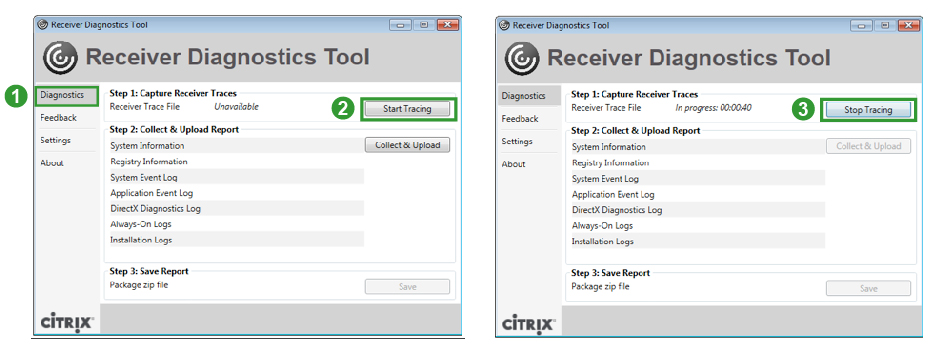
There are a couple methods of logging Workspace app for Windows operations. One method is CTX141751 Citrix Receiver Diagnostics Tool – For Windows, which creates a CDF trace that can be parsed by CDFControl.
Another method is CTX132883 How to Enable Logging on Receiver for Windows Using Registry Entries. The logfiles in %USERPROFILE%\Appdata\Local\Citrix\ are human readable. And CTX206102 Enable SSON Logging Using Registry Key.
Instead of creating the registry keys manually, you can use the following .reg file provided by Wolfgang Thürr:
Windows Registry Editor Version 5.00 ;only for x64 windows os ;import with admin rights ;restart your computer to activate the logging and tracing settings ;create C:\TEMP for the launch ICA log and SSON logn (no environment variables can be used) ;general Workspace app and Receiver logging ;************************ ;logpath: %USERPROFILE%\Appdata\Local\Citrix\Receiver [HKEY_LOCAL_MACHINE\SOFTWARE\ Wow6432Node\Citrix] " ReceiverVerboseTracingEnabled" =dword:00000001 ;Authentication Manager logging ;***************************** * ;logpath: %USERPROFILE%\Appdata\Local\ Citrix\AuthManager [HKEY_LOCAL_MACHINE\SOFTWARE\ Wow6432Node\Citrix\ AuthManager] "LoggingMode"="verbose" "TracingEnabled"="True" "SDKTracingEnabled"="True" ;Self Service logging ;******************** ;logpath: %USERPROFILE%\Appdata\Local\ Citrix\SelfService [HKEY_LOCAL_MACHINE\SOFTWARE\ Wow6432Node\Citrix\Dazzle] "Tracing"="True" "AuxTracing"="True" "DefaultTracingConfiguration"= "global all –detail" ;save launch ICA ;*************** ;logpath: C:\TEMP\ica.log (no environemnt variables allowed) [HKEY_LOCAL_MACHINE\SOFTWARE\ Wow6432Node\Citrix\ICA Client\Engine\Configuration\ Advanced\Modules\Logging] "LogConfigurationAccess"=" true" "LogConnectionAuthorisation"=" true" "LogEvidence"="true" "LogICAFile"="true" "LogFile"="C:\\TEMP\\ica.log" "LogStartup"="true" ;Receiver Always On Tracing ;************************** ;generates ETL Files for analyzing with CDFControl see CTX111961 for details ;can be configured or overruled by GPOs (icaclient.admx) ;path %USERPROFILE%\AppData\Local\ Temp\CTXReceiverLogs [HKEY_LOCAL_MACHINE\SOFTWARE\ Policies\Citrix\ICA Client\AoLog] "EnableTracing"=dword:00000001 ;Single Sign-on Logging ;************************** ;https://support.citrix.com/article/CTX206102 [HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Citrix\Install\SSON] "DebugEnabled"="true" "LogPath"="C:\\Temp"
Troubleshooting – Duplicate Stores
Stores are sometimes duplicated in Workspace app, especially if you are running Workspace app inside a VDA. (h/t Dan High)
StoreFront URLs can be defined in several places:
- In Studio, go to Configuration > StoreFront and delete all URLs configured here.
- Look in GPOs for Computer Configuration > Administrative Templates > Policies > Citrix Components > Citrix Workspace > StoreFront > NetScaler Gateway URL/StoreFront Accounts List. Remove any URLs configured here.
- In the client-side registry, at HKLM\Software\Wow6432Node\Citrix\Dazzle\Sites, you might see store addresses that were specified during a command line installation of Workspace app.
- When Citrix Workspace app switches between StoreFront servers in multiple datacenters, it’s possible for each datacenter to be treated as a separate Workspace app site. This can be prevented by doing the following. From Juan Zevallos at Citrix Discussions:
- Match the Base URL in all datacenters.
- Match the SRID in all datacenters – The SRID can be safely edited in the C:\inetpub\wwwroot\Citrix\Roaming\web.config. Make sure to propagate changes to other servers in the group.
- Match the Delivery Controller names under “Manage Delivery Controllers” – The XML brokers can be different, but the actual name of the Delivery Controller/Farm must be identical.
If you are running Workspace app on a VDA, once you’ve removed the configured URLs shown above, do the following to clean up the VDAs:
- On the VDA, HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Citrix – Delete the number folders representing policy entries.
- On session host VDAs, HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Citrix – Remove the entries for storefront in the following folders.
- Under \receiver\ctxaccount delete all entries.
- Under \SR\Store delete the entries.
- On the VDA, C:\ProgramData\CitrixCseCache – Delete all files
- On the VDA, C:\ProgramData\Citrix\GroupPolicy – Delete all folders and files.
- Run gpupdate and logoff.
- In the user’s registry, HKEY_CURRENT_USER or the profile registry hive. Possible profile reset.
- Under Software\Citrix\Dazzle\Sites – Delete all entries.
- Under Software\Citrix\Receiver\ctxaccount – delete all entries.
- Under Software\Citrix\SR\Store – delete the entries.
- Verify no cached profile folders for user on server.
I am trying to add an account in to Workspace app but when I do, I get “There was a problem with the HTTPS certificate used by Authentication Service”. I am doing this in a lab environment, but cannot get my storefront URL added to the app.
Hi Carl,
Is it possible to do COM port mapping from a local client that is logged into a published desktop and from there they open a published app in another Delivery group (and domain). I can’t get it to work but i’m not sure if it’s even possible to do COM port mapping in a “citrix in citrix” session.
Thanks!
Hi Carl,
Awesome article!
And I have a question about pass through with Netscaler Gateway.
Apart the policy “Single Sign-on for NetScaler Gateway”, any other configuration is required on Netscaler side?
It works for me without any other configuration. Have you tried it?
Yes, I tried. But it didn’t work when I visit NS URL from web..
Hi Carl, How to run similar command from mac ?
CitrixWorkspaceApp.exe STORE0=”AppStore;https://gateway.corp.com#MyStore/Citrix/MyStore/Discovery;On;App Store”
Carl do you know if it is possible to control Client Citrix Receiver/Workspace Settings (Copy/Paste, Drive Redirection) on a per domain / site basis. We connect to internal citrix servers as well as many other vendors and want to control the settings on a per domain basis not just global or by drive “letters”
Something like Client Selective Trust which seems to be based on IE Security zones? https://support.citrix.com/article/CTX133565
Hi Carl,
After updating new citrix workspace version to 1911 and after rebooting the computer, citrix screen appers serveral times, any idea about this?
https://discussions.citrix.com/topic/406200-receiving-a-workspace-screen-after-updating-new-version-1911/
Dear Carl,
One of my clients would like to migrate from XA 6.5 to XA 7.x – however we will not be able to upgrade Citrix receiver from 3.4 to 4.x or workspace 1909 at one night , So please suggest me a version which i can keep accessing both the XA versions for a while until we move things phase by phase
Receiver 4.9 will certainly work.
Receiver 3.4 (PnAgent) might work with StoreFront. For external, old clients won’t support TLS 1.2 ciphers through Citrix Gateway.
Hi Carl,
I love your blog, great collection of useful information.
I am having trouble installing the Workspace app, v1909, as administrator, via GPO using the CheckAndDeployCitrixReceiverPerMachineStartupScript script provided by Citrix. I use a logon script in the Computer Configuration branch of the GPO.
The app installs, and it is in the C:\Program Files (x86)\Citrix\ICA Client, I have specified the ENABLE_SSON=Yes and /includeSSON parameters, yet when I run SSONChecker, it comes back with a big red X saying “Reinstall Citrix Workspace as an administrator and ensure ‘Enable Sungle Sign On’ is checked or use the /includesson…”.
Installing manually as administrator and enabling the SSO checkbox works well.
Also, when using the scripted install, the SSO network provider doesn’t get installed. Installing Workspace manually installs the provider, however it places the SSO provider at the bottom of the list – I have to manually move it to the top, totally counterproductive when having hundreds of workstations to configure.
I searched the Internet but no-one seems to have an answer.
What I’d like to achieve:
– zero-touch installation of the app with SSO support
– Citrix SSO provider moved to the top of the list automatically (as recommended at https://support.citrix.com/article/CTX133982)
Can you please shed some light on what I might be doing wrong.
Thanks,
Zoltan
Here’s a sample script to change ProviderOrder – http://sqlwriter.blogspot.com/2017/03/changing-nic-provider-order.html
If you run the script manually, does it install SSON? If not, then you might have to debug the script to find the problem.
Carl,
Hi, do you know of a way of how to make the citrix receiver logout or pre-logoff so that the profile redirection do not create or bring over ghosted icons or duplicate shortcuts when you log on to a different machine?
We currently using receiver 4.9.700 and profile redirection is turned on for the favorites, documents and desktop, and it is creating duplicate icons or ghosted icons on any machine your profile is logged on to.
Any ideas, comments etc that may help relieve this?
Thank you
Ruben
Maybe this – https://support.citrix.com/article/CTX226454
Hi Carl,
We have bellow strange issue:
Users machine was recently migrated to Windows 10 and when trying to access he Local C Drive from published notepad++ gets error ; “Windows cannot access \\client\c$”. To be more interesting from home user dont get this error. Could it be some local security settings of the win 10 ? user is using receiver i have advised to go to Citrix Workspace
Thnaks in advance !
On the client, in Connection Center, there are options to control access to client drives.
Hi Carl, (Client Selective Trust) is the only solution to avoid annoying security box?
It’s a security/privacy feature for users that might be connecting to untrusted Citrix environments.
I know that but there is a native solution ?
An administrator can remove the prompts by deploying the Client Selective Trust registry keys or group policy to the client devices. https://www.carlstalhood.com/workspace-app-for-windows/#devices
So it’s the only one solution? A co worker think it’s an old solution and doesn’t want use it.
There’s nothing you can do on the server side to prevent the prompts. If you could do that, then users could connect to malicious Citrix environments that disabled the prompts on the server side. The only way for an admin to control the prompts is to configure the client itself, which is what the group policy does.
Another option is to configure Citrix Policy to disable all client device mappings, which would prevent the prompts because nothing is being mapped any more.
Thanks Carl.
Hi Carl, we are using Receiver 4.12 in windows 10 machine , when you removed the access to the applications , icons are still showing in start menu , if users click on those icons , it is give an error while is not available , you to want to remove the shortcut. so how to remove it automatically at user logon ?
What RefreshMs interval is configured? Did you wait for Receiver to refresh? If you manually refresh it, does the icon go away? You can script a refresh by running “SelfService.exe –poll”
No RefreshMs interval is configured. yes , we checked after sometime (like 1hr , 4hr and next day ) after login but still icons were not removed. Even after doing manual refresh also icons are not removed.
Hi Carl, if i read this article : https://support.citrix.com/article/CTX136339
I have to add two keys : hklm+hkcu or two hklm?
I think the HKCU key overrides the HKLM key. I usually only change the HKLM key.
Just one key? WSCReconnectMode “0” ? I made a test with this key and yes hkcu overrides hklm so I have to change the HKCU key.
And what’s about hklm\software\wow…\policies\citrix\dazzle?
Hi Carl,
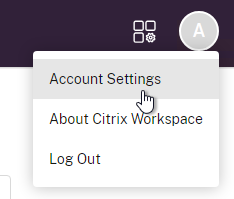
Your guide is just amazing! Well explained. But I couldn’t find one thing or may be it is specified and I don’t see it. How can I activate the workspace app using GPO? manually I can click on activate, it downloads a receiverconfig.cr and when I click on it, it comes up with a pop up and I click on Add and it works fine. But I am not able to do this via GPO. Can you guide me or show me which section in your above guide I should refer to?
Thanks in Advance!
Ash
Group Policy can push the URL to Workspace app. https://www.carlstalhood.com/workspace-app-for-windows/#accounts
Hi Carl,
Hope you are doing well!!
I have a requirement to disable the Citrix receiver toolbar disconnect button from the client windows machine. I need to have clarification whether it is possible or not . if yes, please let me know how can we disable.
Regards,
Ilyas Ahmed
Hello Carl,
I have windows server 2012 with vda 7.18 an workspace app 19.06 installed in window client.
HDX Webcam not working, only usb redirection but with 352*288 resoltuion.
Any suggestion?
Does anyone have the answers to these questions that Carl had in the notes?
“In StoreFront Console, if any configuration changes are performed that affect the Provisioning File, do the Workspace apps / Receivers reconfigure themselves automatically? Or do users have to remove Accounts and re-add (or Reset Citrix Workspace / Receiver) so the updated Provisioning File is imported?”
Been working on fixing an issue and this would be great info to find ahead of my changes. Thanks for any help!
Hi Carl,
Awesome article, was able to get it working with our hybrid environment and it’s working via browser and Citrix Workspace. Just have an issue when I logoff from the browser. I am getting a Microsoft error “An error occurred when we tried to process a WS-Federation message. The message was invalid.” Have you seen this before?
Hi,
Appreciate that this is a very late reply, but I was seeing the same message during logoff and altering the SAML server logout binding from “POST” to “REDIRECT” fixed the problem for me.
Hope that helps,
Matt
Hi Carl,
Workspace App and Beacons question.
XA 7.18 On premise with NS GW for ICA Proxy using Duo Mobile for MFA.
For the Workspace App, I have used Group Policy to add the On Premise URL of the Storefront Server which is https://Storefront.local.mycompany.com.
The URL for the NS GW is https://citrix.mycompany.com
Not sure why, but Workspace App users (1904) configured with the internal storefront entry are able to access the resource remotely from their laptops outside of the LAN.
I know the request is being serviced via the NS GW as the DUO Prompt appears on the handset for secondary authentication.
Is this something to do with my beacon settings as I don’t know why it is actually working?
Tried to add both the NS and SF entries originally but as the base URL is the same, only the SF one was stored.
Any advice would be helpful
Aplogies if this is a duplicate post.
One of my clients is still using Citrix 6.5 and will not give approval to upgrade to the latest version. They are using the the Citrix Secure Gateway and up until now it has worked with the latest versions of the Workspace App. However, beginning with 1904 it no longer works. I’m hoping to get budget approval in the next few months, but until then, I need to keep their clients running the older versions of the workspace app, but I can’t seem to stop it from updating automatically? I’ve tried the settings on a client by client basis and also created a GPO, but nothing seems to work. Any ideas?
Have you tried setting it to LTSR so it only updates with 4.9 versions?
I have not, but I will change that in the GPO and see how it goes. I’ve also tried using the /AutoUpdateCheck=disabled during install on my workstation to see if that works.
Hi Carl,
Do you know if CTX251986 is oldealso forr versions of receiver before 4.9 LTSR, i.e 3.4?
Thanks
Since 3.4 is not supported by Citrix, I couldn’t say, but I would assume it is also affected with no fix forthcoming.
How do i make a Kiosk with Citrix and It lose the Reciever icon in the Taskbar? Any idea.
One option is https://www.thinscale.com/products/thinkiosk/
Another is Citrix Desktop Lock – https://docs.citrix.com/en-us/receiver/windows/current-release/receiver-windows-desktop-lock.html
Hello, How can I use Citrix Common Connection Manager SDK to connect to Storefront from a JAVA Application?
Hi Carl,
Is it possible to logoff the Workspace app after a period of time? We are using mostly Macbooks with the Workspace app and Storefront 3.12. The login stay’s active until you log off, shut down the app or device and we can’t find any setting to change it.
Any Ideas?
We’re on StoreFront 3.12, and there are no GoTo options anywhere in the Store Settings. I was able to finally disable them after finding the Update-DSGenericApplications PS cmdlet after some digging
Update-DSGenericApplications -StoreServiceSiteId 1 -StoreServiceVirtualPath /Citrix/Store -GoToMeetingEnabled $False -GoToWebinarEnabled $False -GoToTrainingEnabled $False
After enabling our StoreFront apps to appear in the Windows start menu, 3 other app shortcuts appeared out of nowhere (GoToMeeting, GoToWebinar, GoToTraining). None of these apps are installed on our XenApp servers or user workstations, and nothing happens if you click on one of those icons, so I’m not sure why they’re there. If I manually remove them they just reappear the next time Workspace refreshes the app list. Is there anyway to get rid of them permanently?
I’m guessing an older version of StoreFront? In StoreFront Console, go to Configure Store Settings and there’s a page to disable the GoTo icons.
We are using 7.15 LTSR and NetScaler Gateway 11.0. User connects to solution via NS and does not have Workspace App or Citrix Reciever installed. The NetScaler will ask to install Citrix Receiver. This installs okay however it installs Citrix Reciever and not the newer Workspace App. We have configured Reciever for Web to use Citrix.com to obtain clients from. Is this normal behaviour? How can we get NS/SF to deploy the latest Workspace App rather than the older Reciever?
It looks like you can edit c:\Inetpub\wwwroot\Citrix\StoreWeb\web.config and set win32 URL to https://downloadplugins.citrix.com/Windows/CitrixWorkspaceApp.exe.
Hey Carl,
do you know, where the issue could be, if you set up a whole fresh Win7 and activate the Screensaver with logon at reactivation?
Screensaver wont kick in.
Registry “setdisplayrequiredmode=0” set
I’ve set the following override:
powercfq requestoverride process gfxmgr.exe
The only thing that happens is: The Window freezes, but the screen wont go dark and lock.
XenDesktop 7.15LTSR and Receiver 4.9.4000.9
Hi Carl
In group policy is it possible to check if the store is already configured on the client machine.
I am pushing out the NetScaler Url/StoreFront account settings via group policy but if the store account settings already exists on the client machine, the user ends up with duplicate stores in his receiver settings.
Thanks
Gary
The store is added to the user’s registry under HKCU\Software\Citrix\Dazzle. Is that what you’re asking?
Hi Carl,
maybe you can help me out there.
Actually we have configured autologin (SSON) to the CAS servers for some users.
Now, when they log on to their client each time after some seconds (when the Workspace App launches) a Windows Sign-In window pops up showing the login progress into the CAS server. After the process finishes the window closes itself.
But I don’t want that window to pop up at all. It’s just irritating for the users.
The login process should just happen silently in the background.
However, I was unable to find something related to that.
Is there any registry key to set that hides this process or suppresses that window?
Thank you in advance!
Hi Carl, can you help me?
I’m implementing peripherals in a Citrix XenApp 7.15.3000 environment, I have a problem with one of them, it’s a HID Omnikey 5022 Smart Card Reader, basically what the device has to do is read the user cards of the company by means of a software (not for authentication) I tried everything, I have an open case with Citrix, but they have not been able to help me. I followed the following tutorial:
https://helgeklein.com/blog/2013/04/getting-smart-card-readers-to-work-with-citrix-xendesktop/
I have tested with Citrix XenDesktop, delivering virtual desktops based on Windows 7 and Windows 10 and it works perfectly, but by Citrix XenApp based on Windows 2012 or 2016 it does not work. Do you have any idea how it could work?
Beforehand thank you very much
Hi Alejandro,
There is no difference in delivering smartcards between XenApp and XenDesktop.
It is not possible to give ultimate working scenario.
I can only recommend few basic setup key points (in advanced setup with specific requirements, e.g. multiple SC from different vendors, some points became complicated to setup):
– it is not necessary to install SC reader drivers in VDA/terminal server
– SC mapping policy must be enabled
– USB mapping for SC reader must be disabled (SC has it own mapping channel)
– SC middleware must be installed in VDA/terminal server (it is not neccessary to install SC middleware on client when client does not use SC directly – e.g. SC is used only for application access inside citrix session not on client)
– you can user certutil -scinfo -silent command as basic troubleshooting (do not be confused with silent option it just skip unlocking card, certutil will just read public infromation from SC)
Petr
I think the new virtual monitor feature does not work on windows server 2012 R2 VDA.
We have tested that but screen resolution is bad on the publish desktop.
What are the prerequisites about VDA OS version ?
thanks
It shouldn’t have any dependency on the VDA since it’s using the same multi-monitor capability built into the VDAs. It only works on a single monitor. DPI is configured correctly?
thanks Carl ! it works perfectly with a single monitor !
we were in dual screen 😉
What is the latest version of Citrix Receiver that can be used again XenApp 6.5 with minimal issues? I tried to look for a document in which Citrix said, in effect, “If you use anything beyond the version of Citrix Receiver, you are more likely to run into problems” but couldn’t find one. In a forum, I saw a Citrix employee make a comment that using more recent versions of Receiver was problematic against 6.5 but then they proceeded *not* to recommend a best and final version. Yes, I am well-aware that 6.5 is out of support.
Hi Carl, any idea on how to suppress the Workspace App FTU on a Mac? All articles seem to point to Windows client only.
If you rename the installer to CitrixWorkspaceAppWeb.dmg then it will not show similar to how installation via RfWeb happens.
Perfect, thank you very much Carl.
Hi All !
I would like to use Receiver Desktop Lock in our environment. As for now we’re using 4.9 CU3 (LTSR), should I use the same level of Desktop Lock or it doesn’t matter as there is no LTSR branch (if I’m not wrong) ?
Thanks for your advice
I think each version of Receiver has its own version of Desktop Lock. Is that what you’re asking?
Thanks for the reply,
I saw that there is a Desktop Lock (DL) for each version of Citrix Receiver
My question was more about to know if I have to respect versions R 4.9 / DL 4.9 or DL can be superior to R
https://docs.citrix.com/en-us/citrix-workspace-app-for-windows/workspace-windows-desktop-lock.html doesn’t say one way or the other. Let’s leave feedback on the Docs article and maybe they will clarify.
I’ll do thanks for the idea — great site by the way
Hello, thank you for everything. I need your advice … We can not configure (but is it possible?) Citrix Workspace App, with as an entry in the “account” field, the alias (alias.mydomain.com) of the address of our Netscaler Gateway instead of the normal address (netscaler.mydomain.com). Do you have any leads to give us?
Users can type in the Gateway FQDN and it should complete discovery successfully. Just make sure Account Services address is configured in the Session Profile.
You can also specify it at the command line. CitrixWorkspaceApp.exe STORE0=”AppStore;https://gateway.corp.com#MyStore/Citrix/MyStore/Discovery;On;App Store”
Yes all work fine with the Gateway FQDN but when we enter the alias FQDN it doens’t work. We try with the alias because the adress is more complicate for our users: the fqdn of the netscaler is netscaler-gateway.domain.com, and we create an alias in our dns ok.domain.com for having an more simple adress. When our customers are not in our place, they can use an internet browser with the adress ok.domain.com and all is ok. We try to enter ok.domain.com in Citrix Workspace App and it doesn’t work, but, when we enter netscaler-gateway.domain.com, it works. is it possible to make it work with ok.domain.com ?(sorry for my bad english, i hope you understand what i mean, and thank you for your responses)
In StoreFront console, did you add a Gateway object using your Alias name and then bind the Gateway to the Store?
Anyone deploying LTSR 4.9 Receiver for Windows and LTSR for MAC with latest updates CU4 via StoreFront using Receiver for Web? I can only find CU1 https://www.citrix.com/downloads/citrix-receiver/additional-client-software/hdx-realtime-media-engine-24.html
Hi Carl
I have two questions regarding an issue with beacon / location detection we have with the Workspace Client for Mac. We have the issue that sometimes the Workspace Client for Mac tries to reach the – unreachable – internal beacon from outside our network for 80 seconds while ignoring the – reachable – external beacons which results in a 80s wait time for the user until he can connect. We do not need the check because all our users connect from the outside (external) through a netscaler gateway to the storefront server – there is no “internal” connection possible…
1. Where are the settings stored on a Mac which are part of the registry on a Windows client and how can they be changed (if not available through the app itself)?
2. Is there a way to disable the whole location checking (internal/external) that the Workspace Client always performs after a network adapter change.
Extract from the ServiceRecord.log client logfile:
[2018-10-11 09:22:05.046] [T0Unknown] [ServiceRecordMain.mm:157] BeaconDetector Routing table changed: Internal ras-storefront.vt.ch expect arrival within 80.000 seconds
[2018-10-11 09:22:05.046] [T0Unknown] [ServiceRecordMain.mm:157] -[BeaconDetector nextCheckID] Internal ras-storefront.vt.ch(540) Connection (0) Start checking
[2018-10-11 09:22:05.046] [T0Unknown] [ServiceRecordMain.mm:157] BeaconDetector Routing table changed: Ignoring External myras.vontobel.com
[2018-10-11 09:22:05.046] [T0Unknown] [ServiceRecordMain.mm:157] BeaconDetector Routing table changed: Ignoring External ping.citrix.com
Every idea to solve this issue would be very much appreciated (the funny thing is that with the Workspace Client for Windows we do not have the issue)…
Regards, Dieter.
Seeing something weird in our environment. 7.15 CU2 VDA on Win10, uninstall Workspace App from the VDA and it removes the Citrix Display Only Adapter and now you can no longer connect to the VDA. The only way I found to fix it is reinstall the Citrix VDA.
Hi Carl,
at the moment I use the Netscaler with otp purely over the web, is it now also possible to get an authentication with the new Workspace App ?
When configuring the Workspace App, it offers me a username / password and passcode, after entering it, unfortunately the login is forbidden.
So I ask myself if the Workspace App supports OTP logins or not?
Thank you and greetings
Thomas
I think native OTP is based on nFactor, which I don’t think is supported in Workspace App, yet. nFactor support was recently added to Gateway VPN Plug-in.
Hi all!
The last few days we have seen an increasing number of users not being able to connect to Xenapp desktop via Storefront.
What we have seen on all affected clients,
Receiver is ver. 4.9
HDX plugin 2.4 is installed
Security update to Flash player has resently been installed KB4343902.
What we also see in event log is this:
Product: Citrix HDX RealTime Media Engine 2.4 — Error 1706. An installation package for the product Citrix HDX RealTime Media Engine 2.4 cannot be found. Try the installation again using a valid copy of the installation package ‘HDX_RealTime_Media_Engine_2.4_for_Windows.msi’.
We fixed It by uninstalling HDX plugin and receiver, and then running “clean up” tool > reboot pc
Then reinstalling receiver and hdx plugin
Do any of you guys have experienced this issue?
Btw. Are HDX plugin integrated in new Workspace client, or Is it still an separate component?
All this material is just flipping amazing. Wow. Crazy good work.
some great articles here btw.
We have issue with one of our Applications when launch using Publish App, user cannot enter the password as they cant see any text they are typing in password field. This issue seem to happen to mobile devices. any ideas
renaming CitrixReceiver.exe to CitrixReceiverWeb.exe prompt for an account 🙁
G’day Carl, I’ve got a problem with Receiver 4.10 and 4.10.1 where if a user does a ‘Send to Desktop’ on an app published to a start menu folder, the resultant icon is removed when the receiver is refreshed. This behavior doesn’t occur in 4.9 and before however. Any ideas?
Just following up re: this. The shortcuts disappear when the user accesses a Citrix application, and this behavior does occur with Receiver 4.9, but only when clean installed. If I installed 4.6, logged in to the Receiver, and then installed 4.9 over the top, the icons would remain. Trying this same method with 4.10 and 4.10.1 didn’t work. Receiver 4.6 has no problems at all.
Hello Stefan, Sorry for the late reply. We had a similar problem. The icon you use for the published application is the problem. It needs to include the following sizes (in px): 16×16, 32×32, 48×48 at a minimum. To accommodate for high dpi devices we also add 128×128, 256×265 and 512×512. Many times even the vendors have only one size for an application icon, which is just laziness, but causes this issue for us. I use icofx3 to merge all the sizes into a single .ico file. We have reported this issue to Citrix in 2017. I believe Citrix Receiver v4.11 might have fixed this issue though?
Hi Carl,
Does Local App Access integrate with Citrix Desktop Lock ? I am able to get LAA and Desktop Lock work separately but not together. Is there something I am doing wrong or is it by design? Thank you for anticipated answer, I just have a client requirement to allow LAA into win7 with Desktop lock installed for their 6.5 environment.
Cheers
Carl,
Just ran into an issue with 4.10.0.16036, it appears to break access to Legacy Xenapp 5 Servers. Was wondering if you have heard or ran into this issue. (Yes I know this has been EOL since 2013)
Anyone had first hand experience of this fixing the authentication popup box which appears randomly. Citrix support have reported it does, don’t want to waste my time testing as I have multiple SDP’s to work on. Thanks.
We have exactly the same problem in our published apps. Combo boxes drop down their list but nothing happens when you click on them while using Receiver 4.10. This is a critical problem for us. We are advising our customers to roll back to Receiver 4.9 but some of them have been receiving automatic updates and are not technically minded enough to handle the rollback well.
Citrix is now investigating.
https://discussions.citrix.com/topic/391635-receiver-410-breaks-sccm-console-context-menu/
https://discussions.citrix.com/topic/391541-receiver-410-dialogpopup-issues/
Thank you Constantin
I have added my notes to that thread there as well.
I hope they fix this client.
Hello Carl,
We have found a bug in 4.10.
Office 2010 document with dropdown select boxes.
Clicking on the box opens the dropdown list but clicking on an item does nothing. You can highlight an item then press “Enter” on the keyboard.
I’m having to rollback to 4.9 as this is not an issue there. I don’t know what other application will be affected by this issue.
Is there a way to prevent BYOD devices from mapping their local drives in a session? But still have internal devices map their drives?
You can do that with SmartAccess. https://www.carlstalhood.com/smartaccess-smartcontrol-netscaler-gateway-12/
Perfect, thanks for clarifying Carl.